Tokenization vs. Encryption: Which Protects Card Data Better
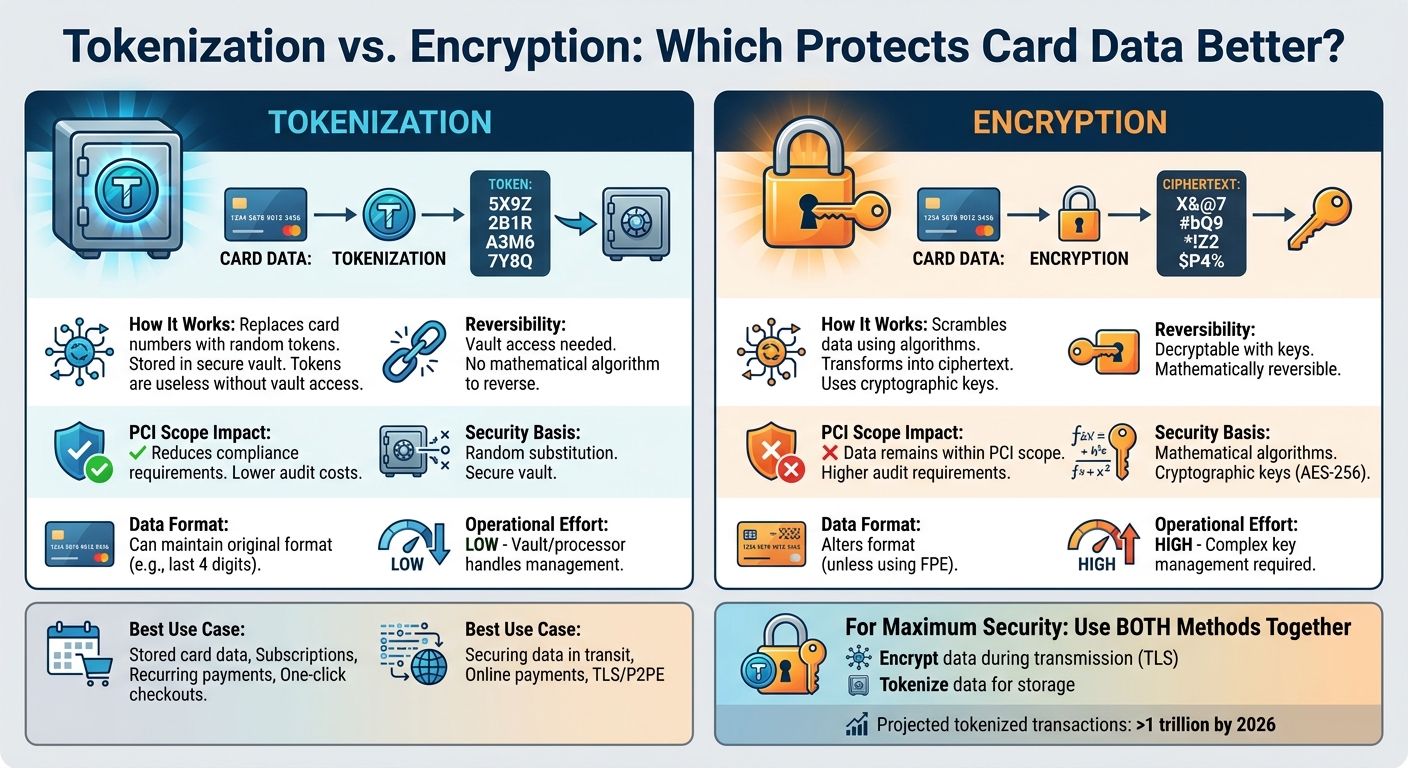
When it comes to protecting cardholder data, tokenization and encryption are two primary methods. Both aim to secure sensitive information but work differently:
- Tokenization replaces card numbers with random tokens stored in a secure vault. Tokens are useless without access to the vault, making this method highly effective for reducing compliance requirements and limiting breach impact.
- Encryption transforms readable data into ciphertext using cryptographic keys. It's ideal for securing data during transmission but requires careful key management to maintain security.
Key Points:
- Tokenization lowers compliance scope and isolates sensitive data, making it valuable for recurring payments and stored card details.
- Encryption protects data in transit and at rest but keeps sensitive information within your system, increasing audit requirements.
- Combining both methods provides stronger security: encrypt data during transmission and tokenize it for storage.
Quick Comparison:
| Feature | Tokenization | Encryption |
|---|---|---|
| How It Works | Replaces data with random tokens | Scrambles data using algorithms |
| Reversibility | Vault access needed | Decryptable with keys |
| PCI Scope Impact | Reduces compliance requirements | Data remains within PCI scope |
| Best Use Case | Stored card data (e.g., subscriptions) | Securing data in transit (e.g., online payments) |
For maximum security, businesses should consider using both methods together.
Tokenization vs Encryption: Key Differences for Card Data Protection
How Tokenization Works
The Tokenization Process
When you check out and enter your card information, the system replaces your 16-digit Primary Account Number (PAN) with a randomly generated token. This token looks similar to a card number - usually 16 characters long and made up of alphanumeric or hexadecimal characters - but it’s completely unrelated to your actual card details.
The original card number is securely stored in a specialized token vault. This vault keeps a one-to-one mapping between the token and the real card number. If a payment needs to be processed, the token is sent to the vault, which retrieves the original PAN through a process known as detokenization. Afterward, the sensitive card data stays locked away in the vault.
The beauty of this system is its simplicity: even if someone breaches your database, all they’d get are meaningless tokens. Without access to the heavily secured and monitored token vault, these tokens are useless and can’t be reversed to reveal the real card numbers. This process forms the foundation for two main approaches to managing tokenization.
Vaulted vs. Vaultless Tokenization
Once you understand the basics of tokenization, it’s important to know the two main approaches:
- Vaulted tokenization relies on storing the actual card data in a centralized, secure token vault. Tokens are assigned randomly, with no cryptographic link to the real card number. By keeping sensitive data separate, this method reduces PCI compliance scope, though it may introduce delays due to the time it takes to look up data in the vault.
- Vaultless tokenization skips the vault entirely and uses cryptographic algorithms to generate tokens. This approach works well for high-volume environments since there’s no need for vault lookups, which speeds things up. However, if the cryptographic keys are compromised, the tokens could potentially be reversed. Additionally, vaultless systems may not reduce PCI compliance scope as effectively as vaulted ones.
For businesses aiming to lower audit costs and limit the impact of breaches, vaulted tokenization is often the go-to choice. On the other hand, vaultless tokenization is ideal for cloud-based systems handling large amounts of data where speed and scalability are key. Both methods improve security and make compliance easier in their own ways.
Benefits of Tokenization
Tokenization offers a range of benefits, all aimed at reducing the risks of data breaches and building trust in payment systems. One major advantage is that it minimizes PCI DSS compliance scope. Systems that only handle tokens - and don’t have direct access to the secure vault - are often excluded from the strictest compliance requirements. This simplifies operations and lowers audit expenses.
Another key benefit is how tokenization isolates sensitive data. By limiting access to the token vault, businesses significantly reduce the potential impact of a breach. As the TIB Finance Team explains, "The critical distinction: there is no mathematical algorithm that can convert a token back to the original card number" [2].
Format-preserving tokenization is another plus. It keeps the structure of the original data intact - for instance, by retaining the last four digits of a card number for receipts while randomizing the rest. This makes it easier to integrate with older systems without disrupting workflows.
With tokenized payment transactions projected to exceed one trillion globally by 2026 [1], more businesses are adopting this approach. It’s particularly useful for securing card-on-file scenarios, enabling one-click checkouts, and supporting recurring billing - all while avoiding the risks of storing sensitive data locally.
sbb-itb-5d40823
How Encryption Works
The Encryption Process
Encryption works by turning readable data, like a credit card number, into an unreadable format called ciphertext. This transformation uses a cryptographic algorithm and a key, effectively "locking" the information. For example, when you check out online, AES-256 encryption scrambles your 16-digit card number into ciphertext. The TIB Finance Team explains it well:
"Encryption transforms readable data (plaintext) into an unreadable scrambled format (ciphertext) using a mathematical algorithm and a cryptographic key" [2].
Unlike tokenization, encryption is a reversible process - anyone with the correct decryption key can unlock and restore the original data.
There are two main types of encryption used in payment systems:
- Symmetric encryption: Uses the same key for both encryption and decryption. It's efficient and often used for securing large amounts of stored data.
- Asymmetric encryption: Involves a pair of keys - a public key for encryption and a private key for decryption. This method underpins secure online communication protocols like TLS.
These two methods address different security needs, particularly in payment systems where both speed and security are critical.
Encryption in Transit vs. At Rest
Encryption plays a key role in protecting card data in two scenarios: during transit and while at rest.
- Encryption in transit: Protects data as it moves from a customer's browser to a payment gateway. Protocols like TLS 1.2 or 1.3 ensure that sensitive information isn’t intercepted by malicious actors. The padlock symbol in your browser’s address bar is a common sign that TLS encryption is active, helping businesses meet PCI DSS Requirement 4.
- Encryption at rest: Secures stored data in databases, backups, or cloud storage. Even if someone gains unauthorized access, they’ll only see ciphertext. For example, PCI DSS requires AES-256 encryption for stored cardholder data. TIB Finance combines TLS for data in transit with AES-256 for stored data, creating a layered defense [2].
In short, encryption in transit prevents eavesdropping, while encryption at rest ensures stored data remains inaccessible to unauthorized users.
Limitations of Encryption
While encryption is a powerful security tool, it’s not without challenges. One of the biggest hurdles is managing the cryptographic keys. If these keys are compromised, attackers can decrypt the data. The 2014 Yahoo breach, which exposed 500 million accounts, demonstrated this risk when poorly managed keys allowed attackers to reverse ciphertext [6].
Jordan Ellis, Senior Payments Content Strategist, points out:
"Encryption protects confidentiality, but it does not automatically eliminate the compliance burden associated with handling cardholder data" [4].
Another limitation is operational complexity. Systems that can decrypt data remain subject to PCI DSS audits, which can increase compliance efforts. Additionally, decryption can slow down system performance and temporarily expose plaintext data - something tokenization avoids entirely.
Encryption is a strong but not flawless tool, requiring careful management to balance security, performance, and compliance.
Tokenization vs. Encryption: Side-by-Side Comparison
Comparison Table: Key Differences
Both tokenization and encryption aim to protect cardholder data, but they achieve this through different mechanisms. Encryption transforms data into unreadable code using mathematical algorithms and cryptographic keys. Tokenization, on the other hand, swaps sensitive data with a random, non-sensitive placeholder that has no direct link to the original data [2][5].
| Feature | Encryption | Tokenization |
|---|---|---|
| Security Basis | Relies on mathematical algorithms and cryptographic keys | Uses random substitution and a secure vault |
| Reversibility | Requires a decryption key | Reversible only by accessing the secure vault |
| PCI Scope Impact | High (encrypted data remains within PCI scope) | Low (tokens are generally out of scope) |
| Data Format | Alters the format (unless using FPE) | Can maintain original format (e.g., last 4 digits) |
| Operational Effort | High (involves complex key management) | Low (vault/processor handles management) |
| Primary Use Case | Protecting data in transit or structured data storage | Reducing PCI scope; recurring billing scenarios |
The Advanced Encryption Standard (AES) with 256-bit keys is widely regarded as the gold standard for encryption, as mandated by PCI DSS for safeguarding stored cardholder data [2][5].
Security and Risk Factors
The table highlights how these methods handle security, but the real test comes during a breach. Tokenization offers a distinct advantage here - if attackers infiltrate your system, they only find meaningless tokens, not usable data. As Marcus Ellery, Senior Payments Security Editor, puts it:
"Tokenization moves trust to a vault or processor, while encryption moves trust to your key management and application security stack" [3].
This distinction makes tokenization particularly effective at isolating sensitive information. It reduces the risk of exposure from breaches or insider mistakes since employees and support teams interact with tokens instead of raw card data [3]. Encryption, while robust, keeps the scrambled data within your system. If encryption keys are compromised, the data can be decrypted.
Recognizing these risk profiles is essential when deciding how to integrate these methods into your security framework.
When to Use Each Method
Choosing the right method depends on your specific needs. Tokenization is ideal for storing customer payment details for recurring transactions, subscriptions, or one-click purchases. These use cases benefit from reduced PCI compliance scope, as highlighted earlier [2][3].
Encryption, on the other hand, is best suited for securing data in transit. Transport Layer Security (TLS) is mandatory for transmitting sensitive data, and Point-to-Point Encryption (P2PE) is particularly effective in retail settings, protecting data from the moment it’s swiped until it reaches the payment processor [2][5].
For the strongest protection, consider combining both methods. Encrypt data during transmission and tokenize it when stored. This layered approach offers enhanced security while minimizing compliance overhead, giving you a solid defense against potential threats [2][5].
Conclusion: Choosing the Right Solution
Key Takeaways
Tokenization offers a way to secure stored card data while easing the burden of PCI DSS compliance. By replacing Primary Account Numbers with tokens, businesses can limit the systems subject to strict compliance requirements. This makes tokenization particularly useful for recurring payments, subscriptions, and one-click checkout processes. On the other hand, encryption ensures data is protected while in transit, using technologies like Transport Layer Security (TLS) or Point-to-Point Encryption (P2PE). It also works well for securing unstructured data, such as files or documents, which don't align with tokenization's structured framework.
The main distinction lies in where trust is placed. As Marcus Ellery, Senior Payments Security Editor, puts it:
"Tokenization moves trust to a vault or processor, while encryption moves trust to your key management and application security stack."
In a tokenization breach, attackers typically gain access only to useless tokens. With encryption, however, compromised keys can expose sensitive information.
These considerations highlight the importance of tailoring your approach to your specific security and compliance needs.
Recommendations for Card Data Security
To maximize card data protection, consider a layered approach. Use tokenization to securely store customer payment details, and rely on encryption to safeguard data as it moves through your systems. This strategy combines the compliance advantages of tokenization with the transmission security encryption provides.
For organizations lacking robust key management capabilities, managed tokenization services can be an effective solution. In retail environments, deploying P2PE at payment terminals can further reduce PCI scope. Lastly, eliminate any unnecessary card data to minimize your overall risk.
Is Payment Tokenization Safer Than Encryption?
FAQs
Do I still need PCI compliance if I tokenize card data?
Tokenization can indeed help narrow the scope of PCI compliance, but it doesn’t entirely remove the need to follow PCI standards. By replacing sensitive card data with tokens, businesses reduce the risk of exposing customer information. However, they are still required to meet PCI guidelines to maintain comprehensive payment security.
Which is safer if my system gets breached: tokens or encrypted data?
Tokenization offers a more secure approach than encryption if your system is compromised. Here's why: tokenization replaces sensitive card data with random, meaningless tokens, which are worthless to attackers. On the other hand, encryption scrambles the data into a coded format, but it can still be decoded if the decryption keys fall into the wrong hands. While both methods improve data security, tokenized data holds no intrinsic value, significantly lowering the risk even if a breach occurs.
How do I choose between vaulted and vaultless tokenization?
Choosing between the two approaches hinges on your specific needs for security, performance, and compliance. Vaulted tokenization relies on a secure, centralized vault to store tokens. While this method simplifies management, it can introduce latency and create a single point of failure. On the other hand, vaultless tokenization dynamically generates tokens without a vault, which mitigates certain risks but demands a more complex setup. Weigh factors like your threat model, scalability demands, and the level of control you require to make the right choice.
