PCI Compliance Simplified: What Every Online Business Needs to Know
PCI compliance is mandatory if you accept credit cards online. It ensures customer data is secure and helps prevent fraud. Non-compliance can lead to fines ranging from $5,000 to $500,000 per month and even loss of the ability to process payments. The latest version, PCI DSS v4.0.1, enforces stricter rules like mandatory multi-factor authentication and enhanced monitoring, effective since March 31, 2025.
Key Takeaways:
- Who Needs It? All businesses handling credit card payments.
- Why It Matters: Protects customer data, avoids fines, and builds trust.
- Costs: Compliance expenses range from $1,000 to $500,000 annually, depending on business size.
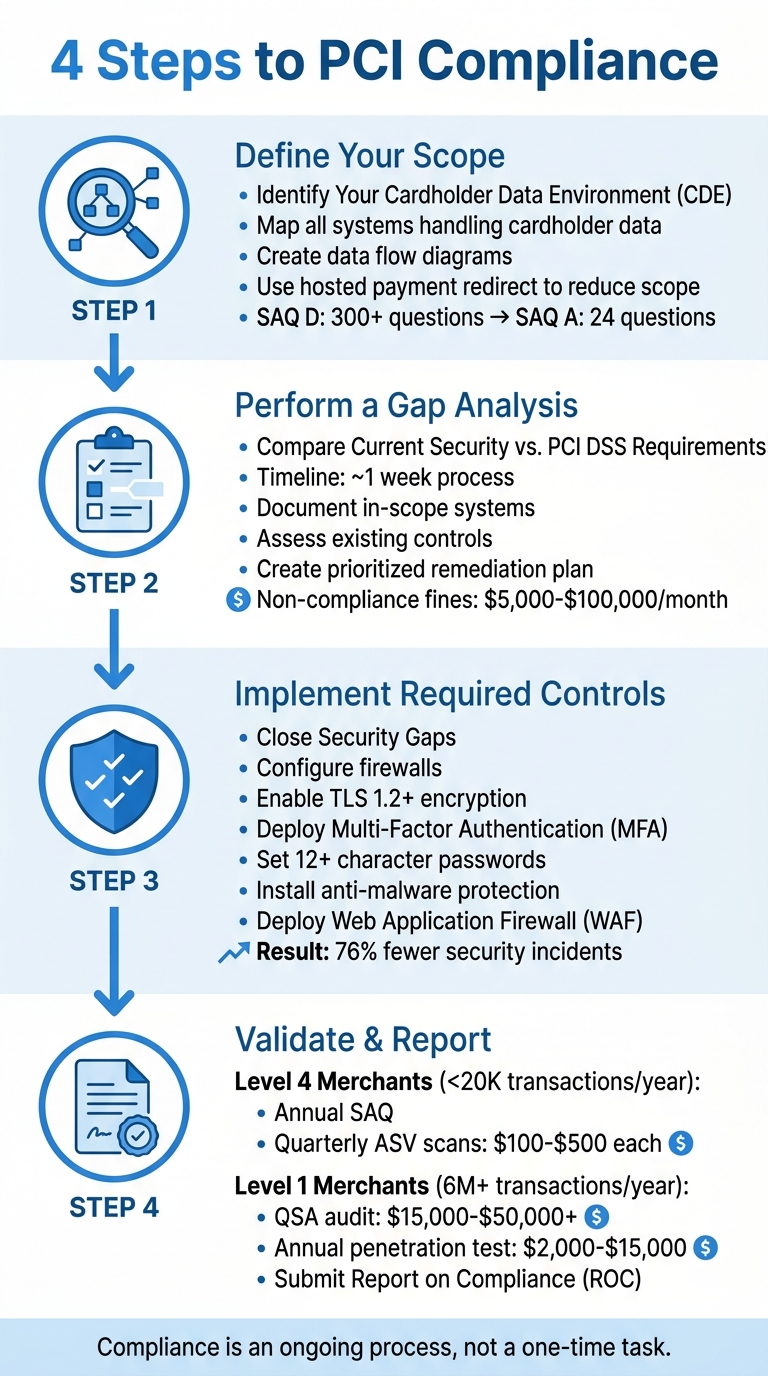
- Steps to Comply:
- Define your Cardholder Data Environment (CDE).
- Perform a gap analysis to identify missing security measures.
- Implement controls like firewalls, encryption, and MFA.
- Validate compliance with assessments or audits.
Compliance is not optional - it’s an ongoing process to secure payment systems and avoid financial and reputational damage.
PCI DSS Explained: A Compliance Guide & Checklist
sbb-itb-5d40823
The 12 PCI DSS Requirements Explained
The 12 PCI DSS requirements are divided into six categories, each designed to create multiple layers of protection for cardholder data. These categories work together to safeguard sensitive information from various threats.
Main Categories of PCI DSS
The PCI DSS framework organizes its 12 requirements into six primary objectives:
- Build and Maintain Secure Networks: This involves setting up firewalls to block unauthorized access and removing default passwords.
- Protect Cardholder Data: Encrypt stored data and secure sensitive information when it’s being transmitted.
- Maintain a Vulnerability Management Program: Use anti-malware tools and ensure systems are regularly patched.
- Implement Strong Access Control Measures: Restrict access to data using role-based permissions, assign unique user IDs with multi-factor authentication (MFA), and enforce physical security measures.
- Regularly Monitor and Test Networks: Keep detailed logs of access, perform quarterly vulnerability scans, and conduct annual penetration tests.
- Maintain an Information Security Policy: Develop comprehensive security policies and provide staff with necessary training.
These measures are critical. For instance, PCI DSS v4.0 now requires passwords to be at least 12 characters long. Multi-factor authentication is mandatory for all access to the Cardholder Data Environment (CDE), not just for remote access. Additionally, audit trails must be retained for 12 months, with the most recent three months readily available.
Let’s explore how these requirements are applied in practical scenarios.
Practical Examples of PCI DSS Controls
Here are some examples of how businesses can implement these requirements:
- Requirement 1 (Firewalls): Configure firewalls to block unauthorized access to payment systems.
- Requirement 2 (Default Passwords): Replace default vendor passwords before systems go live, and disable any unused administrator accounts.
- Requirement 3 (Protecting Stored Data): Use strong encryption methods like AES and consider tokenization, which replaces card numbers with tokens that are useless if intercepted.
- Requirement 4 (Encrypting Data in Transit): Use TLS 1.2 or higher for data sent over public networks, and avoid transmitting card numbers via email.
- Requirement 8 (User Authentication): Assign unique IDs to all employees and contractors, and require MFA for accessing the Cardholder Data Environment.
- Requirement 9 (Physical Security): Protect server rooms and payment terminals with badge readers, surveillance cameras, and secure locks.
- Requirement 11 (Security Testing): Conduct quarterly scans with an Approved Scanning Vendor (ASV) and schedule at least one professional penetration test each year.
Costs for compliance vary significantly depending on merchant level. For example, Level 4 merchants typically spend between $1,000 and $5,000 annually on ASV scans and self-assessments. On the other hand, Level 1 merchants face annual expenses ranging from $200,000 to over $500,000 for Qualified Security Assessor (QSA) evaluations, penetration testing, and necessary remediation tools.
How to Achieve PCI Compliance
4-Step PCI Compliance Process for Online Businesses
Getting PCI compliance right might seem like a big task, but breaking it into four clear steps can make the process much smoother. Here's how you can tackle it effectively.
Step 1: Define Your Scope
Start by identifying your Cardholder Data Environment (CDE). This includes any systems that handle cardholder data, such as hardware, software, and third-party services. A detailed data flow diagram is essential - it should trace the path of payment information from when a customer enters their card details to when it reaches your payment processor.
If you use a hosted payment redirect, you can simplify compliance significantly. For example, this shift reduces your Self-Assessment Questionnaire (SAQ) from the lengthy SAQ D (over 300 questions) to the much shorter SAQ A (just 24 questions). Additionally, network segmentation can help by isolating payment systems from the rest of your network, minimizing the risk of a breach spreading to sensitive cardholder data.
"The single most powerful thing you can do to simplify PCI compliance is to reduce your CDE scope." - Merchant Insiders
Step 2: Perform a Gap Analysis
A gap analysis compares your current security measures to the 12 PCI DSS requirements, helping you pinpoint any missing controls. This process usually takes about a week and involves documenting in-scope systems, assessing existing controls, and creating a prioritized remediation plan.
For many small businesses, the biggest challenge is the absence of documented security policies - a relatively easy and low-cost fix with a big impact. Other common issues include outdated firewall rules, unchanged vendor default passwords, and missing anti-malware software. Addressing these gaps early is crucial, especially since non-compliance fines from card networks can range from $5,000 to $100,000 per month.
Step 3: Implement Required Controls
Once you've identified the gaps, it's time to close them. Here are some key steps:
- Firewalls: Configure them to isolate your CDE.
- Encryption: Use TLS 1.2 or higher to secure cardholder data, both at rest and in transit.
- Multi-Factor Authentication (MFA): Required for all users accessing the CDE under PCI DSS 4.0 - not just administrators.
- Password Policies: Ensure passwords are at least 12 characters long.
- Anti-Malware: Deploy protection and apply patches within 30 days of release.
- Web Application Firewall (WAF): Use it in active blocking mode for payment pages.
- Log Reviews: Automate this process with a Security Information and Event Management (SIEM) system, as manual reviews no longer suffice.
Interestingly, businesses that adopt PCI DSS 4.0 controls report 76% fewer security incidents involving cardholder data.
Step 4: Finalize Validation and Reporting
The final step varies based on your merchant level:
- Level 4 Merchants: If you process fewer than 20,000 e-commerce transactions annually, you'll need to complete an annual SAQ and perform quarterly vulnerability scans with an Approved Scanning Vendor (ASV). These scans usually cost between $100 and $500 each.
- Level 1 Merchants: Those processing 6 million or more transactions annually must undergo a formal audit by a Qualified Security Assessor (QSA) and submit a Report on Compliance (ROC). These audits typically cost between $15,000 and $50,000+ annually. Additional requirements like annual penetration testing can cost between $2,000 and $15,000.
Select the appropriate SAQ type based on your payment processing setup - SAQ A for fully outsourced payments, SAQ A-EP for iframe-based payments, or SAQ D if you store card data. Once completed, submit all documentation to your acquiring bank to maintain compliance and protect your customers' payment data.
Common PCI Compliance Mistakes to Avoid
Navigating PCI compliance can be tricky, and many businesses fall into common traps. Avoiding these pitfalls can help you steer clear of hefty fines - ranging from $5,000 to $100,000 per month - and safeguard your customers' payment data.
Storing Sensitive Cardholder Data
One of the biggest mistakes businesses make is storing sensitive cardholder data that should never be kept. This includes Sensitive Authentication Data (SAD) such as CVV/CVC codes, PINs, and full magnetic stripe data. Even if encrypted, storing this data after a transaction is authorized is strictly against PCI DSS guidelines. Surprisingly, this data often ends up in unexpected places like error logs, debugging files, archived emails, or temporary backups.
"Storing payment card information incorrectly can result in data breaches costing millions in fines, legal fees, and lost customer trust." - PCICompliance.com
The consequences of improper storage can be devastating. For example, in December 2013, Target Corporation suffered a breach that exposed 40 million credit and debit card numbers. Similarly, Home Depot experienced a breach that compromised 56 million customer card numbers.
A better approach? Use tokenization. This process replaces sensitive card data with random tokens that are meaningless to attackers. Tokenization can shrink your PCI compliance scope significantly, potentially reducing your compliance assessment from the rigorous SAQ-D (330 questions, costing $50,000–$300,000+ annually) to the simpler SAQ-A (25 questions, costing $2,000–$5,000 annually). If you must store any data, limit it to the last four digits of the card number - this is allowed under PCI DSS and lowers your risk dramatically.
Additionally, make regular system testing a priority to ensure compliance.
Skipping Regular Security Testing
Compliance isn't a one-and-done task. Treating it as such leaves your business vulnerable to evolving threats. Regular security testing is essential to uncover and address new vulnerabilities as they emerge.
The stakes are high. Global card payment fraud losses surpassed $33 billion in 2025, with eCommerce accounting for 73% of all fraud. On average, a data breach costs $4.88 million, and forensic investigations after a breach can exceed $50,000.
To stay ahead, schedule quarterly vulnerability scans with an Approved Scanning Vendor (ASV). These scans, which cost $100–$500 per quarter, are mandatory for merchants with external-facing IP addresses. Annual penetration tests - costing $2,000–$15,000 - simulate real-world attacks to identify vulnerabilities that could be exploited. Also, conduct scans immediately after major system changes, like software upgrades or network modifications.
| Testing Type | Required Frequency | Cost Range |
|---|---|---|
| External Vulnerability Scan | Quarterly (every 90 days) | $100–$500 per quarter |
| Internal Vulnerability Scan | Quarterly & after changes | Varies |
| Penetration Testing | Annually | $2,000–$15,000 |
| File Integrity Monitoring | Continuous | Included in security tools |
Proactive testing ensures you’re ready to tackle new threats as they arise.
Weak Access Controls
Weak access controls are another common compliance misstep. Using shared admin credentials or relying on single-factor authentication makes it easier for attackers to infiltrate your systems. Under PCI DSS v4.0, Multi-Factor Authentication (MFA) is now required for all users accessing the Cardholder Data Environment (CDE) - not just administrators or remote users.
"If scoping is wrong, everything downstream fails." - Narendra Sahoo, Founder and Director, VISTA InfoSec
To strengthen access controls, assign unique user IDs to all employees and immediately change default vendor passwords on devices like firewalls, routers, and other network components. These small but critical steps not only prevent unauthorized access but also allow you to trace suspicious activity back to specific users. Without robust access controls, your business risks breaches that could cost about $150 per compromised record.
Taking these steps ensures your PCI compliance efforts are thorough and your systems are better protected against potential threats.
AI-Powered Tools for PCI Compliance
Keeping up with PCI compliance manually is no longer practical. Since March 31, 2025, PCI DSS 4.0 has required automated mechanisms for continuous monitoring and log reviews. The days of relying on manual daily checks are over. This is where AI-powered tools come into play, turning compliance into a seamless, ongoing process rather than a sporadic, overwhelming task.
Why does this shift matter? Non-compliance fines can range from $5,000 to $100,000 per month, while the average cost of a data breach is a staggering $4.45 million. AI tools help mitigate these risks by taking over the labor-intensive tasks - monitoring logs, spotting anomalies, and ensuring systems stay compliant without constant human intervention. Let’s dive into how DidIBuyIt uses AI to make this process more efficient.
How DidIBuyIt Supports PCI Compliance
To meet the rigorous standards of PCI DSS 4.0, automation is not just helpful - it’s essential. DidIBuyIt uses AI to simplify secure payment recovery while adhering to strict data security protocols. The platform employs 256-bit SSL encryption to secure data both in transit and at rest, matching the same security standards used by leading banks. This ensures sensitive transaction data remains protected throughout the dispute process.
The AI within DidIBuyIt analyzes transactions and aligns them with specific card network rules - such as Visa 13.1 or Mastercard 4853 - reducing the risk of immediate denials due to incorrect filings. The results speak for themselves: the platform has recovered over $18 million with an impressive 83% success rate across more than 284,000 disputes. For example, in April 2026, a user named Sarah M. recovered $599 from Adobe after being wrongly charged for a canceled subscription. DidIBuyIt built her case in just 4 minutes, and the bank reversed the charge within 6 days.
DidIBuyIt also eliminates the guesswork in chargeback disputes. It automatically generates professional, bank-ready PDF documents complete with evidence checklists and precise reason codes. This feature addresses a major issue, as 60–80% of chargebacks fail due to incomplete or incorrect documentation. Additionally, the platform includes a database of over 50,000 transaction descriptors, allowing businesses to quickly identify unknown charges. By focusing on tokenized data instead of raw cardholder information, DidIBuyIt helps businesses significantly reduce their PCI compliance scope.
Benefits of Using AI for Compliance
DidIBuyIt demonstrates how AI can address the limitations of manual compliance processes. By automating tasks, improving accuracy, and providing real-time insights, AI transforms PCI compliance into a proactive, efficient system. Automated log analysis, for instance, processes massive amounts of data to detect suspicious activity that manual reviews could easily overlook. Meanwhile, continuous monitoring ensures compliance is maintained at all times, rather than being limited to periodic checks.
"AI should assist human assessors, not replace them." - PCI Security Standards Council (PCI SSC)
AI also tackles modern threats that traditional PCI standards weren’t designed to handle, such as prompt injection attacks in chatbots or the risk of AI models memorizing sensitive cardholder data. By leveraging tokenization, AI reduces the need to process raw cardholder information, further narrowing the scope of compliance.
The time savings are another major advantage. DidIBuyIt’s AI-powered tools can process disputes and create a detailed strategy - complete with all necessary documentation - in under 5 minutes. Compare that to the hours of manual research this task would typically require. Even compliance reporting is streamlined, with AI generating professional, bank-compliant documents automatically. This efficiency not only saves time but also ensures accuracy and consistency across all compliance-related activities.
Conclusion
PCI compliance isn't just a box to check - it's a shield for your business and your customers. With global e-commerce sales expected to soar beyond $8.1 trillion by 2026 and the average cost of a data breach hitting $4.4 million, the risks of non-compliance are far too great to ignore. Add to that monthly fines ranging from $5,000 to $500,000 and potential liability costs of up to $90 per compromised record, and the importance of adhering to PCI DSS becomes crystal clear.
Under PCI DSS v4.0.1, compliance has shifted from a once-a-year audit to an ongoing process. This includes automated monitoring, quarterly vulnerability scans, and real-time security controls. Simplifying compliance can be achievable through strategies like using hosted payment pages, adopting tokenization, and incorporating AI-powered tools. These steps not only make compliance more manageable but also strengthen your overall security posture.
"Adhering to PCI compliance standards isn't about avoiding fines. It's about protecting your customers and their personal data." – Shopify
Start by determining your merchant level, reducing your scope with hosted redirects (which can qualify you for SAQ A with just 24 questions), and implementing multi-factor authentication for all administrative access. Don't forget to schedule quarterly ASV scans and maintain thorough documentation - a formal information security policy costs nothing but is essential for audits.
Combining robust security measures with AI-driven automation doesn't just keep you compliant - it builds trust with your customers, ensures business continuity, and defends against the escalating wave of cyber threats. With nearly half of login attempts being malicious and account takeover attacks up 108% year-over-year, prioritizing payment data security is more urgent than ever. By embracing a continuous, automated approach to compliance, you not only meet regulatory standards but also reinforce the trust and stability that are essential to your business's success.
FAQs
What exactly counts as my Cardholder Data Environment (CDE)?
Your Cardholder Data Environment (CDE) consists of everything connected to handling cardholder data. This includes all systems, people, processes, and technologies involved in storing, processing, or transmitting sensitive information such as the Primary Account Number (PAN), cardholder name, expiration date, and service code. Keeping these elements secure is critical to maintaining PCI compliance.
Which SAQ type should my online business use (A, A-EP, or D)?
If your website includes payment pages but depends on third-party processors, go with SAQ A-EP. Use SAQ A if your systems don’t store, process, or transmit cardholder data. For more complex environments that deal with larger volumes of cardholder data, SAQ D is the right choice. Match the SAQ type to your business operations to stay compliant.
How can I reduce PCI scope without hurting checkout conversions?
To keep PCI scope under control while still driving checkout conversions, tokenization is a great solution. By swapping out sensitive card data with secure tokens, you can significantly reduce compliance requirements.
Another effective strategy is working with a trusted payment service provider (PSP) or gateway. These partners can handle much of the heavy lifting when it comes to PCI compliance, easing the burden on your business.
Finally, using streamlined checkout tools can help you stay compliant without compromising the customer experience. A smooth checkout process ensures users stay engaged, helping you maintain strong conversion rates.
