The Anatomy of a Phishing Attack on Banking Customers
Phishing attacks on banking customers are more sophisticated than ever, leading to billions in annual losses. These scams use fake emails, texts, and calls to steal sensitive information and exploit weaknesses in digital communication. Criminals target banking customers because stolen credentials can be quickly converted to cash, often through instant payment platforms like Zelle or Venmo, where recovery is nearly impossible.
Key points:
- Phishing methods: Fake emails, texts (smishing), calls (vishing), and even QR codes.
- Targets: Banking customers due to direct access to funds.
- Tactics: Fake websites, spoofed caller IDs, and real-time interception of credentials.
- Consequences: Financial loss, identity theft, and emotional distress.
- Prevention: Verify messages independently, enable multi-factor authentication (MFA), and monitor account activity.
Phishing remains a major threat, but understanding how these attacks work and staying vigilant can help protect your finances and personal data.
SMS Phishing Attacks Explained: Protect Your Bank Account from Smishing
sbb-itb-5d40823
How Phishing Attacks Work
How Phishing Attacks Work: 3-Stage Attack Process
Phishing attacks are carefully planned operations that exploit weaknesses in digital communication channels, often used by banks and other institutions. These schemes rely on psychological manipulation, technical tricks, and inexpensive resources to achieve their goals. Here's how the process typically unfolds.
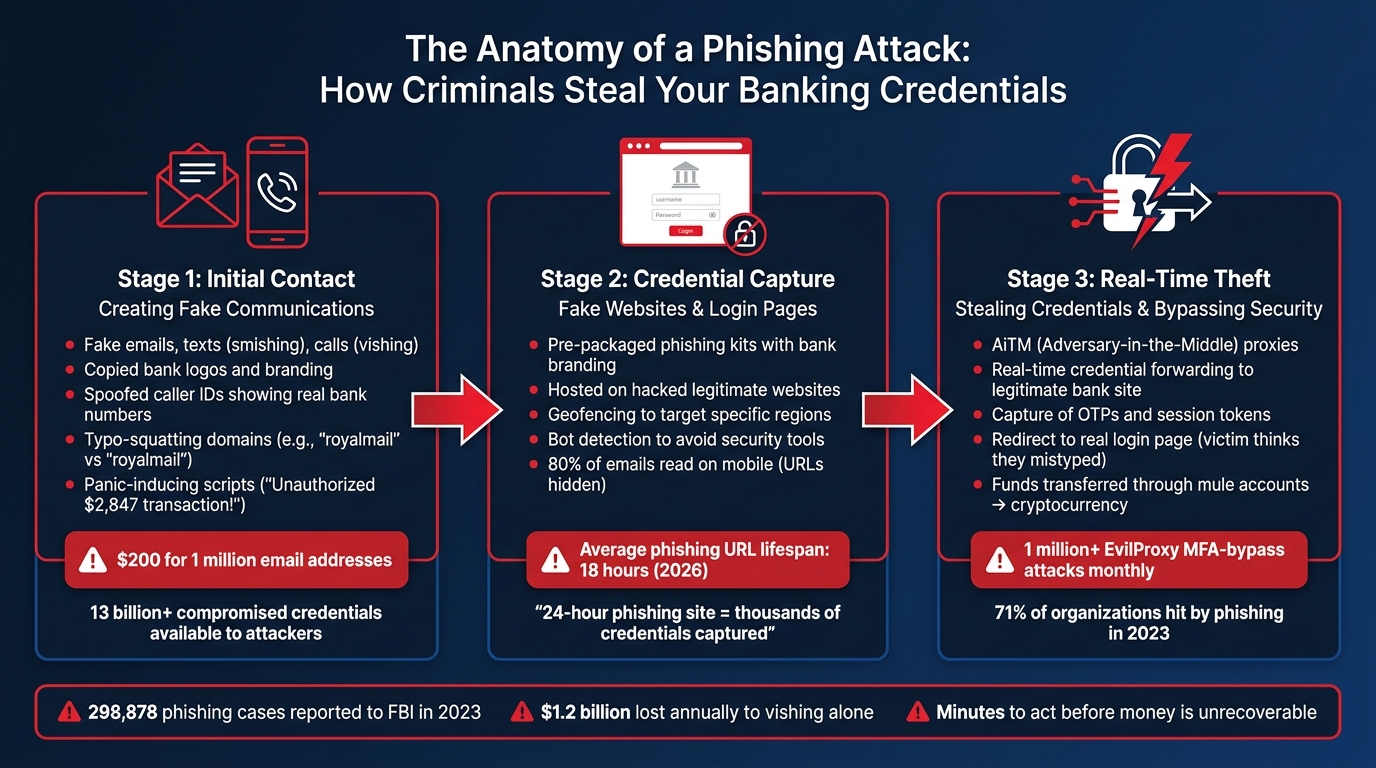
Creating Fake Emails, Texts, and Calls
The first step in a phishing attack involves creating fake communications that look like they come from legitimate sources. Attackers often copy logos and branding directly from a bank's website to make their emails and landing pages indistinguishable from the real thing [2][5]. They also manipulate domain names using methods like typo-squatting - registering domains with slight errors (e.g., "royalmial" instead of "royalmail") - or homograph attacks, which replace Latin characters with similar-looking Cyrillic ones [2][5].
Social engineering is another key element. Scammers rely on data from breaches, such as names, partial account details, or other personal information, to build trust quickly. For instance, databases like Have I Been Pwned catalog over 13 billion compromised credentials from more than 850 breaches, giving attackers a massive pool of potential targets [2]. During a call or text (known as vishing or smishing), scammers often use panic-inducing scripts, such as claiming an unauthorized $2,847.00 transaction has occurred, to pressure victims into acting without thinking [1]. Using VoIP services, they can spoof caller IDs to display the bank's actual customer service number - an effective tactic that costs mere pennies per call [1].
One common trick involves sending a fake fraud alert text, followed by a call impersonating the bank's fraud department. This two-step approach adds an extra layer of authenticity to the scam [1]. As Sherrod DeGrippo, VP of Threat Research and Detection at Proofpoint, points out:
"Threat actors are hoping to evoke an emotional reaction and elicit a click without judgment" [7].
Fake Websites and Login Pages
After grabbing your attention, attackers direct you to fake websites designed to steal your information. These sites are often built using pre-packaged phishing kits - ZIP files containing everything needed to replicate a bank's website, including branding, forms, and even validation scripts [6]. These kits are frequently hosted on hacked legitimate websites, helping them bypass browser warnings and URL blocklists [6].
The cost of running a phishing campaign is shockingly low. For example, a list of one million email addresses can be purchased for about $200, while sending five million phishing texts might cost just $400 in data and 20 hours of automated processing [2]. Modern fake sites also use advanced tactics like geofencing to target specific regions and bot detection to avoid scrutiny from security tools [6]. With 80% of emails now being read on mobile devices - where full URLs are often hidden - these lookalike domains become even harder to detect [2].
Phishing campaigns are increasingly short-lived, with the average URL lifespan dropping from weeks in 2020 to just 18 hours by 2026 [2]. Still, as Saptang Labs explains:
"A phishing site that stays live for 24 hours can harvest thousands of credentials. One that is taken down in two hours might only capture a handful" [5].
Stealing Credentials and Bypassing Security
More advanced phishing attacks use techniques like AiTM (Adversary-in-the-Middle) proxies to intercept credentials and bypass security measures. When you enter your login details on a fake site, the proxy forwards this information to the real banking site in real time. This allows attackers to capture not only your username and password but also one-time passwords (OTPs) and session tokens [3][6].
Between April 14 and 16, 2026, Microsoft Defender Research observed a large-scale phishing campaign targeting 35,000 users from 13,000 organizations. Attackers used "Code of Conduct" themed PDF attachments to lure victims into a multi-stage process. This included CAPTCHA challenges to bypass automated defenses, leading to an AiTM session hijacking that captured authentication tokens [8]. Each month, over 1 million attacks using the MFA-bypass tool "EvilProxy" are launched, and in 2023, 71% of organizations reported falling victim to at least one phishing attack [7].
Once your credentials are stolen, many phishing kits redirect you to the legitimate login page, making it seem like you simply mistyped your password [6]. Meanwhile, the attackers may already be inside your account, transferring funds. These stolen funds often pass through "mule accounts" - frequently belonging to students or elderly individuals - before being converted to cryptocurrency, making them nearly impossible to trace. This multi-layered approach demonstrates the complexity and effectiveness of modern phishing schemes.
What Happens After a Phishing Attack
When attackers get hold of your banking credentials, the consequences can be swift and devastating. Financial losses can occur within minutes, and the personal aftermath often lingers far longer.
Fraudulent Transactions and Account Access
Once inside your account, scammers waste no time. They initiate unauthorized transactions - like wire transfers or Zelle payments - moving your money to mule accounts. From there, the funds are often converted to cryptocurrency, making them nearly impossible to trace. Take the case of a 70-year-old retiree in Mountain View, California, who lost $25,000 in September 2024. A scammer posing as her bank used a spoofed caller ID to gain her trust, transferred the money to a mule account, and quickly converted it to cryptocurrency. In another instance from late 2024, a Virginia woman lost over $700,000 - her entire life savings - through a series of fraudulent wire transfers, some even conducted in person at a Wells Fargo branch [9].
Modern phishing kits are even more dangerous. They can capture one-time passwords (OTPs) in real time, allowing criminals to bypass two-factor authentication and make high-value purchases on legitimate retail sites. If they gain access to your password manager, the damage can escalate as they compromise every linked account.
"Once the money is transferred from your account, you have not days, not hours, but minutes to report it, to have hope of getting something back."
– Thomas W. Cronkright II, Co-founder and Executive Chairman, CertifID [9]
The chances of getting reimbursed by your bank are slim. In 2023, major U.S. banks had abysmally low reimbursement rates for scam victims: JP Morgan Chase reimbursed only 2%, Wells Fargo 4%, and Bank of America 24%. Many claims are denied under the Electronic Fund Transfer Act if the customer "authorized" the transaction under false pretenses [9]. These sophisticated, fast-paced attacks highlight the need for better fraud recovery systems.
Identity Theft and Data Misuse
Phishing attacks don’t just empty bank accounts - they also steal personal data, leading to identity theft and credit fraud. Attackers often harvest Social Security numbers, birth dates, and addresses, which are then sold on dark web marketplaces. A single banking login can fetch thousands of dollars, fueling crimes like synthetic identity theft and fraudulent loan applications [2].
In 2023, phishing topped the FBI's Internet Crime Complaint Center (IC3) list, with 298,878 reported cases [10]. Voice phishing, or vishing, alone cost Americans over $1.2 billion annually [1]. Meanwhile, UK Finance reported £1.1 billion in fraud losses in 2024, with over £600 million stolen in just the first half of 2025. Experts believe the actual numbers are two to three times higher due to underreporting [2].
Financial and Emotional Impact
The damage doesn’t stop at financial losses. Victims often face additional costs, like bank fees for fraudulent transactions, credit monitoring services, and fees for freezing and reissuing cards. Fraudulent applications can also tank credit scores, making it harder to secure loans, rent apartments, or even get certain jobs.
Emotionally, the toll can be just as severe. Victims often experience prolonged stress, sleepless nights, and anger over falling for the scam. Cathy M., a victim, shared her ongoing frustration:
"I am still finding it hard to sleep at night, mulling over what made me believe him, and what exactly happened. I am angry." [9]
U.S. Senator Richard Blumenthal criticized banks for their lack of action:
"The banks are aware that, every single day, some of their customers are going to be hurt. But they are failing to protect consumers from threats." [9]
| Bank | 2023 Scam Reimbursement Rate |
|---|---|
| JP Morgan Chase | 2% |
| Wells Fargo | 4% |
| Bank of America | 24% |
The FBI’s "Financial Fraud Kill Chain" offers some hope. It can freeze fraudulent wire transfers of $50,000 or more if reported within 72 hours. But most victims don’t realize they’ve been scammed until it’s too late [9].
How to Spot and Avoid Phishing Scams
Understanding the dangers of phishing is only half the battle - knowing how to spot and avoid these scams is just as important. Scammers rely on urgency and fear to trick their victims, so taking a moment to examine any unexpected message can save you from falling into their trap. The key is to stay alert and recognize the warning signs before you click, call, or share sensitive information.
Warning Signs of Phishing
Phishing messages are often designed to create panic. They might claim your account is "on hold", "compromised", or has a "billing problem", pushing you to act without thinking. However, legitimate banks don’t operate this way - they won’t pressure you or request sensitive information like your PIN, online banking password, or one-time access codes via email, text, or phone. If you encounter such a request, it’s a major red flag.
Carefully inspect the sender’s details. Emails from addresses that don’t match the official domain (e.g., not ending in "@wellsfargo.com") or ones that use generic greetings like "Dear Customer" instead of your name are likely phishing attempts. Look out for grammar mistakes, awkward phrasing, or unusual instructions, such as being told "do not call us." These subtle clues can reveal a scam.
"Phishing stands out as the simplest yet most potent cyber-attack, chiefly targeting the most susceptible yet powerful element: the human mind."
– Adam Kujawa, formerly of Malwarebytes Labs [11]
Once you’ve identified these red flags, the next step is to confirm whether the message is legitimate.
How to Verify Suspicious Messages
Never rely on the contact information provided in an unsolicited message. Instead, use trusted sources, like the phone number printed on the back of your credit or debit card or your bank’s official mobile app, to verify the message.
If you’re unsure about a website, the FDIC BankFind Suite can confirm whether it belongs to an FDIC-insured bank [14]. Before clicking any link, hover over it to check its actual destination. Watch for slight misspellings or odd domains, such as a bank name appearing as a subdomain. For added safety, type your bank’s URL directly into your browser or use a saved bookmark instead of clicking links in messages.
"When asked to 'act immediately,' do the opposite. Go slow and resist the urge to respond right away."
– Wells Fargo [12]
If someone calls and pressures you to stay on the line or discourages you from hanging up, it’s likely a scam. Hang up immediately and call your bank using an official number to confirm.
Security Tools and Protection Methods
While staying vigilant is critical, having the right tools in place can provide an extra layer of protection. Multi-factor authentication (MFA) is one of the best defenses against phishing. By enabling MFA, you’ll need both your password and an additional credential - like a code from an authenticator app or a fingerprint scan - to log in to your banking accounts [13].
A password manager can help you create and securely store strong, unique passwords for all your accounts. Additionally, set your devices to update automatically to ensure you’re protected by the latest security patches. Regularly review your bank statements and enable mobile app alerts to quickly catch any unauthorized activity.
If you suspect phishing, take action. Forward suspicious emails to reportphishing@apwg.org and texts to 7726 (SPAM). You can also report fraud attempts to the FTC at ReportFraud.ftc.gov. In 2024 alone, consumers reported losing $12.5 billion to scams, with email being the most common way scammers contacted their victims [13][14].
Recovering Lost Money with AI-Powered Tools
Even with the best preventive measures, breaches can still happen. When they do, acting quickly to recover lost funds is critical. Falling victim to phishing doesn’t mean all is lost - disputing charges promptly can make a huge difference. However, 60%–80% of chargebacks fail because people use the wrong reason codes or lack proper evidence to support their claims [15]. This is where AI-powered tools step in, helping consumers not only detect phishing but also reclaim their money effectively.
Finding Fraudulent Charges
Start by carefully reviewing your bank statements for any charges you don’t recognize. Even small transactions can be a red flag - scammers often test stolen credentials with minor charges before making bigger withdrawals. File a dispute as soon as possible. While most banks allow up to 120 days, major U.S. banks like Chase, Bank of America, and Wells Fargo often enforce stricter timelines, such as a 60-day window for certain disputes [15][16].
To strengthen your claim, gather key evidence, including:
- Screenshots of phishing messages
- Timestamps showing when you discovered the fraud
- Communication records with the merchant
- Proof that you didn’t authorize the transaction
Additionally, save any cancellation emails, order confirmations, or notes from phone calls. These details can make or break your case.
How DidIBuyIt Helps with Disputes
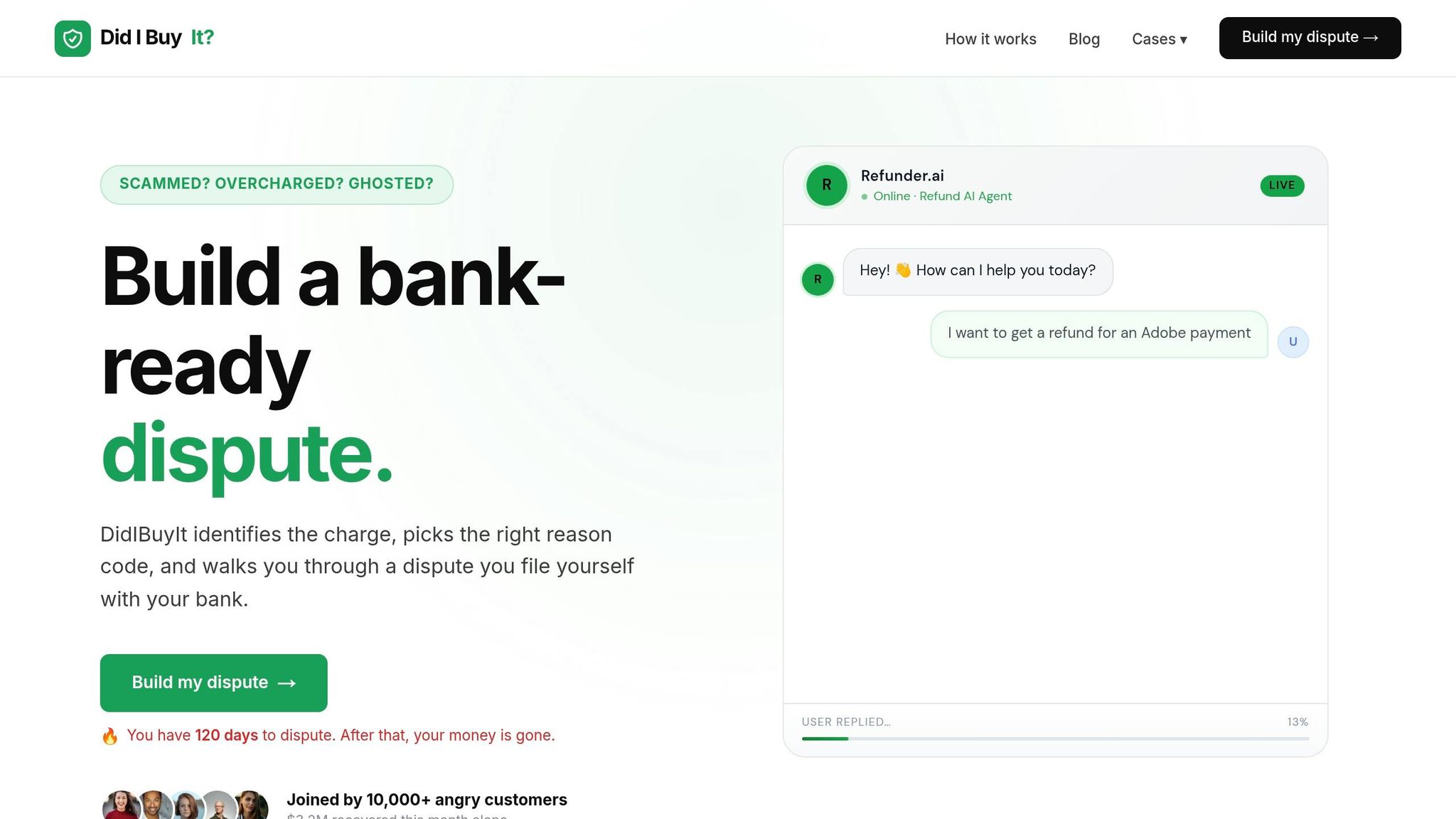
DidIBuyIt uses AI to simplify the dispute process by identifying the correct card network reason code, such as Visa 13.1 or Mastercard 4853 [15][16]. Incorrect codes are one of the main reasons banks reject claims [15]. The platform also checks banking regulations to ensure your dispute meets all necessary requirements [17][18].
When you use DidIBuyIt, you’ll get a bank-ready dispute package that includes:
- A PDF with your dispute details
- Call scripts for speaking with your bank
- A checklist of required evidence
The platform even provides guides for over 4,200 banks and credit unions, including the "Big 6" institutions [16]. For example, Nina W. successfully recovered $920 in just 11 days after refiling her denied Airbnb dispute using the correct reason code provided by DidIBuyIt [15]. Once a properly documented dispute is filed, banks often issue provisional credit vs final credit within 5 to 10 business days [17].
You can choose a plan that fits the complexity of your dispute.
DidIBuyIt Plan Comparison
| Plan | Price | Best For | Key Features |
|---|---|---|---|
| Basic Recovery | Flat Fee | Standard fraud disputes | AI dispute analysis, bank-ready documents, step-by-step guidance, encrypted data handling, support for Visa/Mastercard/Amex/PayPal |
| Advanced Support | Flat Fee | Complex or high-value cases | Includes Basic features plus 24/7 priority support, enhanced evidence preparation, and real-time tracking |
Both plans also give you access to DidIBuyIt’s 50,000+ descriptor database and general bank chargeback guides. The AI drafts dispute letters and assigns reason codes in minutes, providing a cost-effective alternative to traditional legal services [17].
Conclusion
Understanding phishing attacks and their methods is a critical part of securing your banking information. These attacks often rely on creating a sense of urgency, invoking authority, or instilling fear to bypass your better judgment. As ScamSignal aptly states, "Defenders have to be right every time, attackers only need to be right once" [2]. Spotting red flags - like generic greetings, poor spelling, or messages pushing you to act immediately - can help you stay ahead of these threats. Always take a moment to hover over links to verify their actual destination before clicking [7, 34].
For added safety, type your bank's URL directly into a browser or use the official app. Consider using a password manager that avoids auto-filling credentials on suspicious or lookalike sites, which can alert you to potential fraud [7, 10]. Strengthen your accounts with multi-factor authentication, preferably through authenticator apps or hardware keys, as SMS-based methods are more vulnerable to interception.
If you think you've been targeted, respond quickly. Forward suspicious emails to your bank’s abuse address (e.g., abuse@bankofamerica.com) and delete them immediately [19]. Keep a close eye on your statements for any unauthorized charges, even small ones, as scammers often test stolen information with minor transactions.
When disputing fraudulent charges, using the correct reason code is key. DidIBuyIt’s AI tool simplifies this process by identifying the correct Visa or Mastercard reason code and generating complete dispute packages ready for submission. The platform is compatible with a wide range of banks and provides tailored guidance for major institutions like Chase, Bank of America, and Wells Fargo.
While phishing kits have become more advanced, incorporating features like bot detection and real-time credential capture [4], your everyday habits remain your best defense. Stay cautious, verify independently, and act quickly if something feels suspicious. By combining vigilance with strong security tools and recovery platforms, you create a robust defense against the evolving threat of phishing.
FAQs
Can I get my money back after a Zelle or wire scam?
If you've been a victim of fraud, you might have a chance to recover your money by reporting the incident to your bank and requesting a chargeback. This approach tends to work best for unauthorized transactions, as banks often have limited options for reversing payments that you approved. It's crucial to act quickly - reach out to your bank as soon as possible to get advice on how to proceed.
What type of MFA is safest for my bank account?
Passkeys are considered the most secure form of multi-factor authentication (MFA) for protecting your bank account. They rely on public key cryptography, which makes them extremely effective at preventing phishing attempts and credential theft. This cutting-edge approach ensures your financial details remain safeguarded from many common online threats.
What should I do in the first 10 minutes after clicking a phishing link?
To minimize harm, take immediate action. Start by disconnecting your device from the internet to prevent any ongoing malicious activity. Next, update passwords for any accounts that might have been affected, focusing on those tied to the device or the suspicious link. Lastly, keep a close eye on your bank accounts and financial statements for any unauthorized transactions to detect and address possible fraud quickly.