Card-Not-Present Fraud: Detection Patterns Merchants Miss
Card-not-present (CNP) fraud is a growing problem for merchants, costing businesses billions annually. With global e-commerce sales rising, fraudsters are finding new ways to exploit weak points in outdated detection systems. Here’s what you need to know:
- CNP fraud losses are projected to hit $28 billion by 2026.
- Fraudsters use tactics like rapid small transactions (card testing), synthetic identities, and device spoofing to bypass security.
- Traditional systems often fail to detect these patterns due to fragmented data and static rules.
Advanced tools, like AI-driven systems, can analyze behavior, transaction velocity, and device data in real time to spot fraud more effectively. When fraud does occur, platforms like DidIBuyIt simplify dispute recovery, helping merchants recover lost revenue quickly. To stay ahead, businesses need to combine smarter fraud detection with efficient recovery processes.
Fraud Prevention Tips: What is Card-Not-Present (CNP) Transaction
sbb-itb-5d40823
Detection Patterns Merchants Frequently Overlook
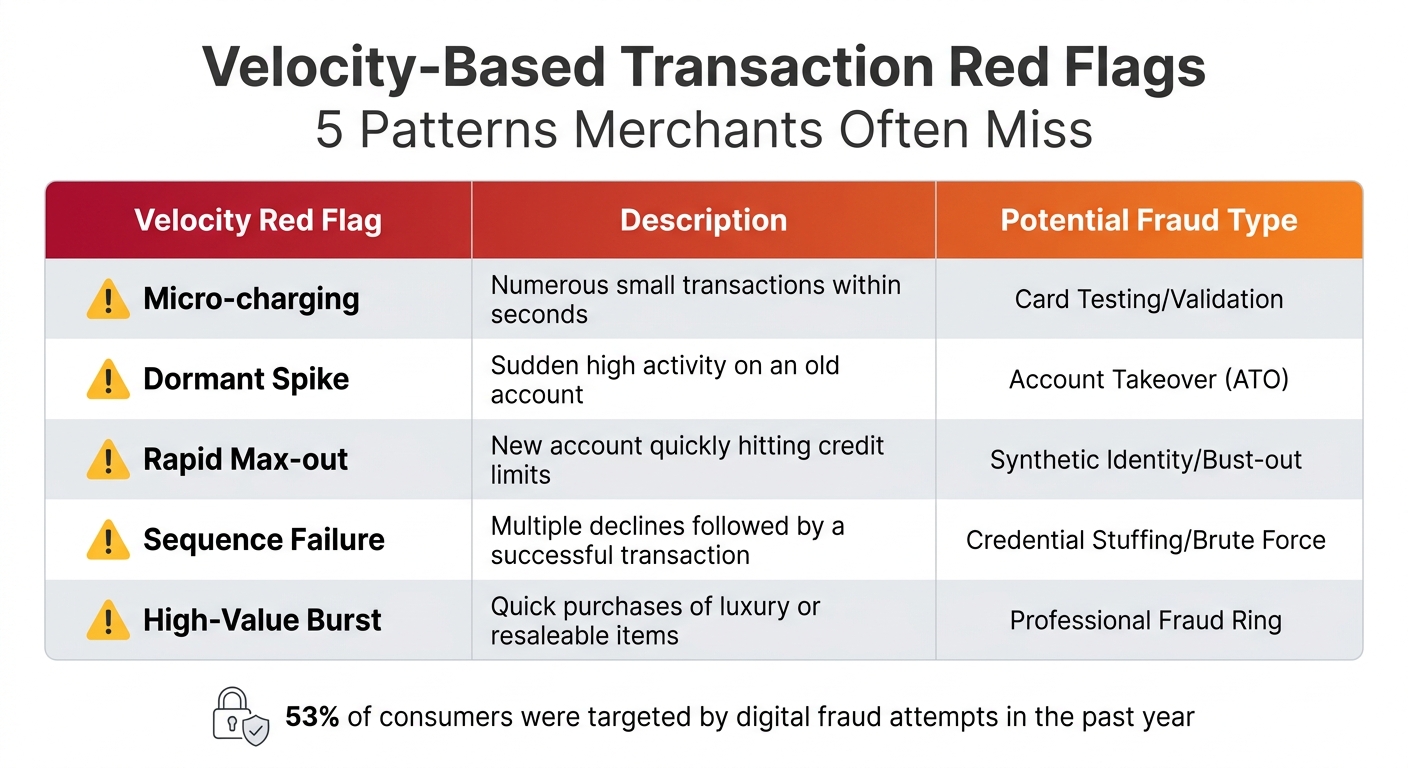
5 Velocity-Based Transaction Patterns That Signal Card-Not-Present Fraud
Fraudsters often take advantage of overlooked gaps in detection systems, sidestepping basic card and identity checks by relying on subtle behavioral tactics.
Velocity-Based Transaction Patterns
Transaction velocity refers to how quickly and frequently purchases are made. Fraudsters tend to act fast because stolen card data becomes useless once the cardholder notices unauthorized activity and blocks the card. Recognizing these patterns is key to spotting fraud.
For instance, card testing is a common strategy where fraudsters make several tiny transactions - sometimes just a few cents - to confirm whether a stolen card is active. Once they verify the card works, they quickly move on to larger purchases. Similarly, a dormant account that suddenly processes a flurry of transactions can signal an account takeover. Another example is bust-out fraud, where a new account is rapidly maxed out with high-value purchases. Alarmingly, fraud prevention data shows that 53% of consumers were targeted by digital fraud attempts in the past year [2].
Merchants often miss these warning signs due to fragmented systems - fraud, risk, and customer experience teams may not share data in real time. Additionally, businesses might hesitate to tighten velocity limits, fearing they’ll flag legitimate customers during busy periods.
| Velocity Red Flag | Description | Potential Fraud Type |
|---|---|---|
| Micro-charging | Numerous small transactions within seconds | Card Testing/Validation |
| Dormant Spike | Sudden high activity on an old account | Account Takeover (ATO) |
| Rapid Max-out | New account quickly hitting credit limits | Synthetic Identity/Bust-out |
| Sequence Failure | Multiple declines followed by a successful transaction | Credential Stuffing/Brute Force |
| High-Value Burst | Quick purchases of luxury or resaleable items | Professional Fraud Ring |
Behavioral Anomaly Signals
Fraudsters often behave differently than legitimate customers. For example, navigation anomalies - like completing forms at machine speed, skipping checkout steps, or visiting unusual site sections - can indicate automated or scripted activity. In contrast, genuine users tend to browse, pause, and sometimes abandon their carts.
Other red flags include inconsistent shopping behavior and the use of disposable email addresses. If a customer typically shops via mobile but suddenly makes a high-value purchase on a desktop, this could warrant further investigation. Fraudsters also favor disposable email addresses (e.g., "asdfg789h@disposablemail.net") to avoid leaving a trace [2].
Geographical mismatches are another critical clue. For example, a customer using a UK-issued Visa card from a British Telecom IP address in London is low risk. But the same card being used from a data center IP in another country - especially through a VPN - raises serious concerns [3].
"Relying solely on identity-based checks is no longer sufficient. To stay ahead, businesses must closely observe how customers behave in real time, rather than just who they are." – Team Bureau [2]
Device and IP Spoofing Techniques
Fraudsters often use tools like VPNs, proxies, and device emulators to hide their real location and identity. This can create discrepancies between the IP address, billing address, and card-issuing country. Connections from Tor exit nodes or data center IPs (like those from AWS or Google Cloud) are particularly suspect [4].
Another clear sign of fraud is impossible travel - when the same account shows activity from two far-apart locations, like London and Tokyo, within hours. No legitimate user could travel that quickly.
Device fingerprinting offers another layer of security by creating a unique identifier based on hardware and software details like screen resolution, browser type, and operating system. Even if a fraudster clears cookies or changes their IP address, their device fingerprint often remains the same. For example, in early 2026, FlightHub introduced device intelligence measures that reduced their false positive rate by 6%, leading to smoother bookings and fewer abandoned carts [5].
"Fraudsters are skilled at recycling credit cards, identities, and email addresses. But one thing they can't constantly spin up? Their device." – Proof [5]
VPN usage should be treated as a risk factor, not an automatic red flag, since many legitimate customers use VPNs for privacy. However, Tor exit nodes deserve extra scrutiny because of their strong association with fraud. Ultimately, combining multiple signals - IP location, device details, behavioral patterns, and transaction velocity - into a single risk score is essential for effective fraud detection. A real-time, integrated approach is the best defense against these diverse tactics.
New Fraud Tactics That Complicate Detection
As anti-fraud measures get tougher, criminals are upping their game with more complex, multi-platform schemes. These tactics often mimic legitimate transactions, making them harder to spot. By exploiting trust and leveraging cross-platform coordination, fraudsters continue to stay one step ahead.
Triangulation Fraud and Shadow Storefronts
Triangulation fraud is a particularly deceptive scheme that involves multiple parties, making it tough to trace. Here’s how it works: fraudsters set up fake online storefronts offering massive discounts. When a customer places an order, the fraudsters collect payment and personal details. Then, they use stolen credit card information to buy the item from a legitimate retailer and ship it to the customer [8].
The trick? The customer receives their order, so they’re none the wiser. The fraud only comes to light when the real cardholder notices the unauthorized charge and files a chargeback. In the end, the legitimate merchant is left to deal with the financial loss [8].
"In Triangulation fraud, fraudsters just sit in the middle and move stolen money through a real transaction." – Shivam Agarwal, Head of Go-to-Market Strategy, Signzy [6]
The scale of these operations is staggering. In 2024, one criminal network managed over 75,000 fake e-commerce sites, scamming more than 800,000 shoppers and processing over $50 million in fraudulent orders over three years [8]. For merchants, the financial toll is enormous, with losses from triangulation fraud alone reaching between $660 million and $1 billion every month [6].
These schemes underline the importance of developing more advanced detection strategies that can keep pace with evolving fraud tactics.
Infrastructure-Based Fraud Convergence
Fraudsters are also leveraging coordinated networks and shared resources to carry out their schemes. This approach involves a criminal supply chain that includes aged merchant accounts, stolen card data, and forged business documents [8].
One common tactic is purchasing established businesses or aged merchant accounts. These accounts often come with higher transaction limits and a clean processing history, helping fraudsters bypass security checks. Another method is transaction laundering, where payments for illegal businesses - like unlicensed pharmacies or gambling sites - are funneled through legitimate-looking accounts. To payment processors, these transactions appear as standard retail sales [8].
The financial impact is massive. By 2025, U.S. merchants were losing an average of $4.61 for every dollar of fraud, once you factor in investigation costs, fees, and other expenses [9]. Meanwhile, the dark web continues to provide a steady supply of stolen data, with 269 million card records posted online in 2024 alone [8].
These sophisticated fraud networks highlight the pressing need for AI-powered tools to tackle increasingly complex schemes.
Using AI-Driven Tools to Improve Fraud Detection
AI-powered tools are transforming fraud detection by addressing the limitations of traditional, rule-based systems. These advanced systems can process massive datasets in real time, identifying patterns and anomalies that human reviewers or static rules might overlook. Machine learning models evaluate a wide range of signals - like payment velocity, device fingerprints, typing patterns, and unusual behaviors - to assign a risk score between 0 and 100 in just 100 milliseconds [15]. With access to millions of transactions across global networks, these models adapt to ever-changing fraud tactics, offering more effective solutions for fraud prevention and improving the overall customer experience.
Benefits of AI in Fraud Prevention
AI-driven systems bring a level of precision and insight that traditional methods simply can't match. By analyzing hundreds of data points at once, AI can detect subtle fraud signals that would otherwise go unnoticed. The financial benefits are striking: businesses using machine learning tools report up to a 40% increase in fraud detection accuracy [11]. Additionally, 83% of industry leaders say AI has drastically reduced false positives and customer churn [12]. False declines - a major issue for merchants - are projected to cost $443 billion in lost revenue by 2025, nearly ten times the cost of actual fraud [15]. Even more concerning, 33% of consumers abandon a retailer permanently after a single declined transaction [13].
"By automating fraud management, businesses can quickly respond to emerging threats, improve customer trust and accept more good transactions without adding unnecessary friction." – John Munn, Head of Global Data Science, Visa [10]
AI-powered tools also tackle challenges like fraudsters masking their IP addresses with VPNs. Using device fingerprinting, these systems collect unique hardware and software data - such as battery level, screen resolution, and WebGL attributes - to identify returning fraudsters, even if they change locations [13]. Advanced techniques like graph neural networks go a step further by mapping relationships between accounts with similar device fingerprints, exposing coordinated fraud rings [11].
How AI Tools Identify Fraud in Practice
Real-world applications show how AI tools excel in identifying fraud with remarkable accuracy. Behavioral biometrics, for instance, monitor subtle user interactions like typing speed, mouse movements, and navigation habits to differentiate humans from bots. Fraudsters using automated scripts often display unnatural behaviors, such as perfectly straight mouse paths or unrealistically fast typing speeds, which AI systems flag immediately.
Visa's Decision Manager offers a compelling example. In 2023, it screened 3.2 billion transactions and prevented an estimated $33 billion in potential fraud losses [10]. This system uses consortium intelligence, leveraging data from Visa's global network to identify fraudsters who have targeted other merchants. For instance, a stolen card's device fingerprint can alert businesses to similar fraudulent attempts across thousands of platforms.
AI also excels at detecting synthetic identities - fake accounts that mimic legitimate user behavior over time. These accounts may browse, make small purchases, and build trust before launching large-scale attacks, a tactic that traditional systems often miss. AI, however, monitors post-transaction behavior, such as refund patterns or "item not received" claims, to uncover friendly fraud and refund abuse weeks after the initial purchase [14].
Additionally, AI handles velocity attacks - where fraudsters make rapid, small transactions to test card validity - by identifying unusual patterns before significant damage occurs. It also flags behavioral shifts, like a legitimate user suddenly making high-value purchases from a new country at odd hours, which static systems might overlook or misinterpret. By continuously adapting to new fraud tactics, AI tools shift fraud detection from reactive to proactive, offering real-time solutions that protect businesses and customers alike.
How DidIBuyIt Helps with Dispute Recovery and Prevention
Even with advanced AI tools improving fraud detection, effective dispute recovery is critical to protect merchant revenue. When card-not-present (CNP) fraud bypasses detection systems, merchants often face chargebacks and financial losses. DidIBuyIt’s AI-powered platform tackles this issue by streamlining dispute recovery and helping businesses spot fraudulent transactions early. In May 2026 alone, the platform processed over 50,000 dispute cases, recovering $3.2 million [17]. Let’s explore how DidIBuyIt supports both recovery and prevention.
How DidIBuyIt Simplifies Dispute Recovery
DidIBuyIt uses AI to analyze transaction data and determine the best dispute strategy in under three minutes [16][18]. It reviews bank regulations, card network rules, and merchant policies to select the most effective approach for each case. The platform automatically assigns the correct reason code - like Visa 13.1 or Mastercard 4853 - a crucial step since 60–80% of chargebacks fail due to incorrect codes or incomplete evidence [19].
The system also generates bank-compliant dispute letters, evidence packages, and PDFs tailored to specific financial institution requirements [16][17]. By calculating success probabilities based on historical data and current rules, DidIBuyIt provides step-by-step guides, including scripts for bank calls and emails to merchants [17][18]. For example, in April 2026, Raj K. used the platform’s recommended reason code and script to recover a $1,840 overcharge from Microsoft Azure, securing bank approval [19].
Protecting Your Business with DidIBuyIt
Timely action is essential in dispute recovery, as merchants must meet the 120-day dispute deadline to avoid permanent fund losses [17]. DidIBuyIt’s charge identification tool simplifies confusing transaction descriptions in seconds, helping prevent disputes caused by customers failing to recognize legitimate charges - a frequent cause of false CNP fraud claims [17].
The platform’s evidence checklist ensures merchants gather all required documentation - like shipping records, invoices, and communication logs - before disputes escalate [16][17]. In one case from May 2026, Nina W. recovered $920 from Airbnb after initially being denied. She identified the error using DidIBuyIt, corrected the reason code, and resubmitted her claim with proper evidence, receiving approval in just 11 days [19]. With 94% of users recovering funds they didn’t realize they were owed, DidIBuyIt transforms dispute recovery into a systematic process that safeguards revenue [17].
Conclusion: Improving Your Defense Against CNP Fraud
In 2023, CNP fraud accounted for 73% of card fraud, leading to global losses of nearly $9.5 billion [1]. Fraudsters exploit overlooked patterns like velocity anomalies, device spoofing, and behavioral inconsistencies - gaps that traditional detection methods often fail to address. Basic browser-based tools are no match for sophisticated antidetect software, which can cost as little as $200 per month and easily bypass these defenses [20].
To tackle this, businesses need to move beyond standard signals. Advanced tools such as card-level intelligence - including BIN analysis, AVS/CVV codes, and 3DS outcomes - are critical [20]. AI-powered solutions can further reduce fraud by combining behavioral analytics, persistent device tracking, and cross-merchant velocity monitoring [1]. For instance, one international airline cut fraud by an impressive 97% and reduced resolution times from 8 hours to just 2 hours using automated systems. Similarly, an electronics retailer slashed its fraud rate from 11% to 0.2% [7].
When fraud does slip through, DidIBuyIt's AI-driven platform simplifies dispute recovery. It analyzes transaction data, assigns accurate reason codes, and prepares bank-compliant evidence packages, ensuring lost revenue is recovered efficiently. This streamlined approach strengthens overall fraud defenses when initial detection isn’t enough.
A robust strategy combines real-time insights with effective dispute recovery processes. Treating browser data as supplemental, while prioritizing detailed acquirer data and multi-axis geo-correlation, helps catch even the most advanced fraud tactics [20]. As AI solutions become more widespread, staying ahead of evolving threats is critical. Businesses that stick to outdated methods risk undetected fraud losses averaging 1.8% of their revenue [21].
FAQs
What velocity rules should I set without blocking good customers?
To ensure legitimate customers aren’t mistakenly blocked, avoid setting velocity thresholds that are too strict, as they can lead to false declines. Instead, lean on adaptive decision-making by analyzing key signals such as device reuse, email domain trends, and historical risk profiles.
It’s also important to regularly review and fine-tune your rules to avoid unnecessary complexity, which can increase false positives. Striking the right balance between fraud prevention and a smooth customer experience means creating flexible, behavior-driven rules and committing to ongoing optimization.
How can I tell a real customer on a VPN from a fraudster?
Distinguishing real customers using a VPN from potential fraudsters requires a close look at patterns like geolocation and behavior. For instance, legitimate users typically connect from consistent locations, with IP addresses that align with their billing address or the one associated with their payment card. On the other hand, suspicious signs might include IPs tied to data centers or locations that don’t match the customer’s usual activity.
Behavioral clues are also key. Watch for things like unusually fast transactions or device details that don’t add up. At the same time, it’s important to recognize that some privacy-conscious users rely on VPNs, so these factors should be weighed carefully.
What evidence do I need to win a CNP chargeback fast?
To handle a CNP (Card-Not-Present) chargeback efficiently, it's crucial to present clear evidence that the transaction was valid. This might include documents like proof of customer authorization, delivery confirmation, and accurate transaction details. These pieces of evidence show that the purchase was authorized and completed as expected, strengthening your case.
