PCI DSS 4.0: What Changed and Why Compliance Costs Rose
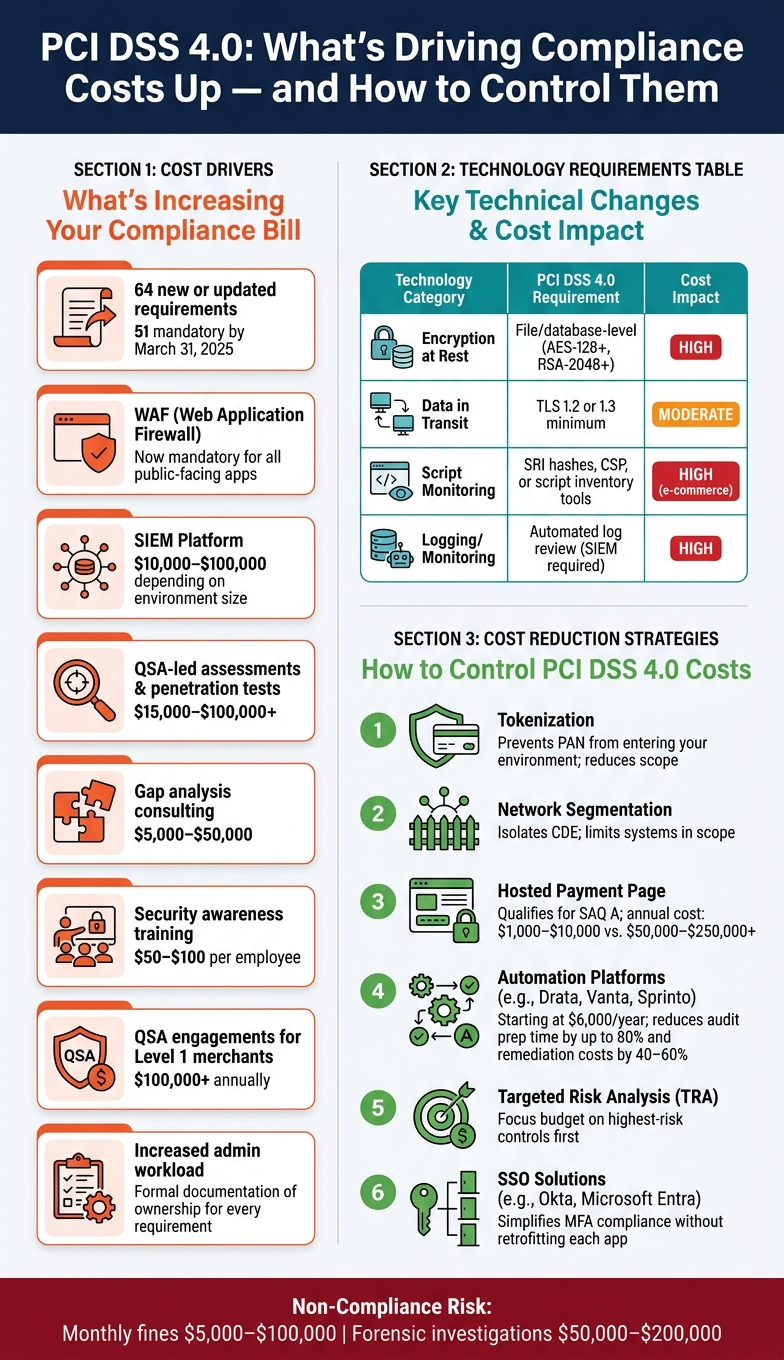
PCI DSS 4.0 introduces 64 new or updated requirements, with 51 becoming mandatory by March 31, 2025, significantly increasing compliance costs for businesses handling payment card data.
Key changes include stricter authentication, enhanced monitoring, and a shift to continuous security practices. These updates aim to address evolving threats but require substantial investments in tools, labor, and documentation. Here's what you need to know:
- Multi-Factor Authentication (MFA): Now required for all access to cardholder data.
- Password Policy: Minimum length increased to 12 characters.
- Encryption Standards: Stronger encryption for stored data and stricter monitoring of payment page scripts.
- Customized Compliance: Offers flexibility but demands more documentation and testing.
- Third-Party Oversight: Expanded accountability for vendors and service providers.
These updates mean higher costs for tools like Web Application Firewalls (WAFs), Security Information and Event Management (SIEM) systems, and vulnerability scanning. Businesses must also allocate resources for gap analyses, risk assessments, and staff training. However, strategies like automation, tokenization, and network segmentation can help control expenses while maintaining compliance.
From Confusion to Compliance: Navigating PCI DSS 4.0 with Fortra
sbb-itb-5d40823
Key Structural Changes in PCI DSS 4.0
PCI DSS 4.0 introduces three key shifts that reshape how organizations manage security: a transition to continuous compliance, a new flexible validation path, and stricter oversight of third-party providers. These changes form the backbone of the updated technical and procedural requirements that contribute to higher compliance costs.
Security as a Continuous Process
Under previous versions, compliance was often treated like a one-time, annual test. PCI DSS 4.0 changes this mindset by requiring organizations to treat security as an ongoing, year-round effort instead of a periodic assessment [3][1]. To support this, the new version mandates that every security control has clearly defined and documented roles, ensuring accountability is maintained consistently rather than only during reviews [3][10].
Another major addition is the Targeted Risk Analysis (TRA), which allows businesses to adjust the frequency of their security activities based on assessed risks [1][2]. This approach not only makes compliance more dynamic but also emphasizes proactive risk management.
Alongside this shift to continuous oversight, PCI DSS 4.0 introduces greater flexibility in how organizations can achieve compliance.
The New Customized Approach to Compliance
Previously, the only option for compliance was the Defined Approach, which required organizations to follow prescribed controls. Now, PCI DSS 4.0 introduces the Customized Approach, which gives businesses the option to implement alternative, tailored controls to meet security objectives [8][2]. Unlike compensating controls, which were used only when specific requirements couldn't be met, the Customized Approach is a forward-thinking alternative that allows for proactive customization.
However, this flexibility comes with added responsibilities. As Saravanan G from Glocert International explains:
"The customized approach is not a shortcut - it requires more documentation, risk analysis, and rigorous testing than the Defined Approach."
- Saravanan G, Glocert International [13]
The Customized Approach is only available for organizations undergoing a Report on Compliance (ROC) assessment and cannot be applied to Self-Assessment Questionnaires (SAQs) [12]. For each customized control, a full TRA must be conducted and documented [11][2]. This means businesses need to invest significant time and effort into additional testing and paperwork. To streamline this process, it’s crucial to involve a Qualified Security Assessor (QSA) early on, ensuring the alternative controls are properly validated [1][2].
Expanded Scope and Third-Party Responsibilities
Outsourcing payment processing doesn’t exempt merchants from compliance obligations. Under PCI DSS 4.0, businesses must document which requirements are handled by their Third-Party Service Providers (TPSPs) and which responsibilities are shared [14][5]. Additionally, every TPSP’s Attestation of Compliance (AOC) must be re-verified annually, and vendor contracts must explicitly acknowledge the provider's compliance duties [14].
For instance, a retail client discovered 41 scripts on their checkout page, far exceeding the 17 they initially counted. This highlights the importance of monitoring all third-party scripts on payment pages [15]. Requirement 6.4.3 specifically holds merchants accountable for ensuring the integrity and authorization of every third-party script [15]. As Vicky Duehr, Director of Compliance at NMI, puts it:
"One important change in PCI DSS 4.0 is an expanded focus on minimizing risk from any TPSPs you use... you are ultimately responsible for everything within your PCI compliance scope." [9]
Another critical update is the formalization of scope validation. Organizations are now required to document and confirm their PCI DSS scope at least once a year, as well as after any significant changes to their environment [10].
Technical and Procedural Changes That Drive Up Costs
The updates in PCI DSS 4.0 emphasize continuous and thorough security measures, but they come with a price. These technical and procedural changes often require significant investments in tools, labor, and time, driving up compliance costs.
Stricter Authentication and Access Control Requirements
The new requirements for multi-factor authentication (MFA) now extend to all users accessing the Cardholder Data Environment (CDE), including internal help desk staff [1][3]. This means businesses may need to purchase additional MFA licenses for every employee interacting with systems linked to the CDE. Additionally, password policies have become more rigorous: the minimum password length has increased from 7 to 12 characters (or 8 if the system cannot support 12) [3][11]. Hard-coded passwords in scripts, configuration files, or application code are also no longer allowed [1][4], necessitating extensive code reviews and fixes.
"The new controls are not technically hard. They are organisationally hard." - Daniella Mitchell, The BrightByte [7]
Organizations can simplify compliance with these requirements by implementing a Single Sign-On (SSO) solution, like Okta or Microsoft Entra, in front of internal CDE applications. This approach helps meet Requirement 8.4.2 without the need to retrofit each application individually [7].
Beyond access controls, updates in encryption standards add another layer of complexity and cost.
New Data Protection and Encryption Standards
PCI DSS 4.0 introduces tougher standards for securing stored card data. Full-disk or partition-level encryption is no longer adequate for protecting Primary Account Numbers (PAN) [13]. Instead, businesses must adopt file-level or database-level encryption, which often requires substantial infrastructure upgrades. Requirement 6.4.3 also mandates monitoring of payment page scripts, requiring organizations to inventory, justify, and actively track every script [13][18].
| Technology Category | PCI DSS 4.0 Requirement | Estimated Cost Impact |
|---|---|---|
| Encryption at Rest | File/database-level (AES-128+, RSA-2048+) | High - significant infrastructure upgrades |
| Data in Transit | TLS 1.2 or 1.3 minimum | Moderate - protocol/software updates |
| Script Monitoring | SRI hashes, CSP, or script inventory tools | High for e-commerce - new requirement |
| Logging/Monitoring | Automated log review mechanisms | High - SIEM or equivalent tools required |
Broader Monitoring and Vulnerability Management Rules
Two major updates in monitoring requirements significantly impact operations. First, internal vulnerability scans must now be authenticated, meaning scanners must log into systems to identify vulnerabilities that unauthenticated scans might miss [1][4]. Michele Daryanani, Partner of Cyber Security at KPMG Switzerland, notes:
"The requirement to have authenticated internal vulnerability scans will force IT security teams to set up credentialed vulnerability scans for all eligible assets and remediate new vulnerability findings – a task challenging under existing patch management procedures." [4]
Second, manual log reviews are no longer sufficient. Requirement 10.4.1.1 mandates automated mechanisms for log reviews [1][12]. For organizations without a Security Information and Event Management (SIEM) system, this means investing in software that can cost anywhere from $10,000 to $100,000, depending on the size of their environment [17].
Furthermore, Payment Page Tamper Detection (Requirement 11.6.1) requires tools to detect unauthorized changes to HTTP headers and payment page content at least weekly [12][15]. Since many internal teams lack the expertise for this, businesses often need to adopt specialized SaaS tools to meet this requirement.
Why Compliance Costs Are Going Up
PCI DSS 4.0 Compliance Costs: Tools, Staffing & Scope Strategies
The technical changes discussed earlier don’t just exist as theoretical challenges - they come with real financial implications. Every new requirement adds to your compliance budget, and these costs can quickly pile up across tools, personnel, and processes.
More Requirements Mean Higher Costs
With PCI DSS 4.0, compliance has grown more demanding, introducing 64 new or updated requirements, 51 of which become mandatory on March 31, 2025 [1][12]. These changes spark a cascade of expenses for gap analyses, remediation, and ongoing documentation efforts.
One major cost driver is the increased administrative workload. Each requirement now includes a sub-requirement to formally document ownership and responsibilities [1]. For a mid-sized organization, this means revising policies, updating job descriptions, and adjusting responsibility matrices across dozens of controls - a process that can take weeks of internal labor.
"PCI DSS costs accumulate from validation, security tooling, testing, remediation, and ongoing internal management." - Alexandra Dolia, Akurateco [19]
On top of that, these additional requirements often necessitate significant investments in technology.
Technology Upgrades and System Changes
The updated controls under PCI DSS 4.0 demand both technical and procedural shifts. For instance, Web Application Firewalls (WAFs) are now mandatory for all public-facing web applications under Requirement 6.4.2, eliminating the previous option to use manual code reviews [1][5]. Organizations that relied on manual reviews now have no choice but to implement WAFs.
Another example is the requirement for automated log reviews (Requirement 10.4.1.1). Businesses without a Security Information and Event Management (SIEM) platform must now invest in one. Additionally, QSA-led assessments and penetration tests come with hefty price tags, often ranging from $15,000 to over $100,000 [19].
"For many organizations, meeting PCI DSS v4.0's requirements will require overhauling systems for advanced encryption, stronger authentication, and enhanced data protection." - ACI Worldwide [20]
Staffing and Overhead Demands
Beyond technology, operational changes add even more to the compliance bill. Meeting the new requirements often necessitates dedicated staff for tasks like risk analyses, evidence documentation, and ongoing compliance management.
The Targeted Risk Analysis (TRA) requirement (12.3.1) exemplifies this shift. It requires businesses to create a formal risk-based justification for the frequency of specific security activities [1]. As Voss Intelligence explains:
"Think of targeted risk analysis as the PCI Council saying 'we trust you to make intelligent decisions, but you need to show your work.'" [1]
To manage these tasks, businesses may need to hire in-house teams or rely on external consultants. Gap analysis consulting alone can cost between $5,000 and $50,000, depending on the complexity of the environment, while QSA engagements for Level 1 merchants can exceed $100,000 annually [16]. Security awareness training adds another layer of expense, costing $50 to $100 per employee [17].
How to Manage PCI DSS 4.0 Compliance Costs
The costs mentioned earlier are real, but they don't have to spiral out of control. With a thoughtful approach, most organizations can maintain compliance without exceeding their budget.
Prioritize Controls Based on Risk
Focusing on high-risk areas is key. TRA (Requirement 12.3.1) allows organizations to direct their budget toward the riskiest areas instead of spreading resources thinly across all controls [1][10].
For instance, web application attacks are still the top cause of retail breaches. This makes Requirements 6.4.3 (script management) and 11.6.1 (tamper detection) excellent starting points for many merchants. Addressing these areas not only helps meet compliance but also reduces breach-related expenses [7]. As Daniella Mitchell, author of The BrightByte Playbook, explains:
"The new controls are not technically hard. They are organisationally hard." [7]
Once high-risk controls are addressed, integrating automation can make compliance even more efficient.
Use Automation and AI Tools
Automation is a practical way to cut costs while improving compliance processes. For example, Requirement 10.4.1.1 requires automated log reviews, which encourages many organizations to adopt automation platforms [12][18].
Nazar Tymoshyk, CEO of UnderDefense, highlights the benefits:
"Organizations that automate PCI compliance evidence collection reduce audit preparation time by up to 80% and cut remediation costs by 40–60% versus manual approaches." [22]
Platforms like Drata and Vanta, which have high ratings on G2, simplify evidence collection and gap analysis. Pricing starts at around $6,000/year (for Sprinto) and goes up to $12,000/year (for Hyperproof) - a small fraction of the cost of manual remediation [18]. Additionally, automated tools for script monitoring can help meet Requirements 6.4.3 and 11.6.1 without increasing staffing needs.
Reduce Scope Through Tokenization and Network Segmentation
Another effective way to manage costs is by reducing the scope of compliance. Alexandra Dolia of Akurateco puts it succinctly:
"The fastest predictor of PCI compliance cost is scope." [21]
Two proven methods for reducing scope are tokenization and network segmentation. Tokenization ensures the PAN (Primary Account Number) doesn't enter your environment, while network segmentation isolates the Cardholder Data Environment (CDE). This minimizes the number of systems in scope, cutting both validation and remediation expenses [6][17].
For smaller merchants, using a hosted payment page can significantly lower compliance costs. This approach often qualifies businesses for SAQ A, the simplest and least costly validation method. Annual compliance costs can then stay between $1,000–$10,000, compared to the $50,000–$250,000+ required for larger, in-scope environments [21][17]. By capturing card data at the edge and routing it directly to a secure proxy, organizations can ensure the PAN never touches their backend systems, keeping their scope as small as possible from the outset [6].
Conclusion: How to Handle PCI DSS 4.0 Without Overspending
PCI DSS 4.0 introduces 64 updated or new requirements - 51 of which become mandatory by March 31, 2025. These updates bring increased cost pressures for mid-size and enterprise merchants. Key changes like continuous monitoring, expanded multi-factor authentication (MFA), stricter authentication measures, and new e-commerce security rules (such as Requirements 6.4.3 and 11.6.1) significantly impact compliance budgets.
This shift moves the focus from annual audits to maintaining ongoing security, which reshapes how costs are distributed. The real financial burden lies in consistently meeting these controls. As Payrails explains:
"PCI DSS 4.0 is no longer about passing a point-in-time audit – it's about showing that controls work every day." [6]
Businesses that treat compliance as a once-a-year effort often face last-minute expenses, rushed fixes, and delays in product launches. On the other hand, those embracing continuous compliance - through automation, network segmentation, and tokenization and encryption - can better control their costs and avoid unnecessary financial strain.
The risks of non-compliance are steep. Monthly fines range from $5,000 to $100,000, while forensic investigations can cost between $50,000 and $200,000 [2]. Joe Wise, Head of Marketing at Verisave, puts it plainly:
"Security is mandatory. Paying unnecessary penalties is not." [23]
To manage these challenges, merchants can implement proactive strategies. Tools like DidIBuyIt help streamline payment-related processes, ensuring better organization and documentation. When combined with scope reduction, targeted risk analysis, and automation platforms, these measures make PCI DSS 4.0 compliance more achievable without breaking the bank.
FAQs
What PCI DSS 4.0 changes impact my business the most?
PCI DSS 4.0 brings some notable changes aimed at strengthening security measures and offering more flexibility in how businesses meet compliance standards. Here’s what stands out:
- Stricter Authentication Rules: Multi-factor authentication (MFA) is now mandatory for all access to the cardholder data environment (CDE). Additionally, password requirements have become more stringent to enhance security.
- Customized Approach: This new option allows businesses to meet security objectives in ways that best suit their environments. However, it comes with a catch: companies must provide detailed documentation and validation to prove compliance.
- Future-Dated Requirements: Some updates are designed to be implemented over time, giving businesses a chance to adapt gradually.
- Focus on Continuous Security: The new framework emphasizes ongoing security practices rather than one-time compliance efforts.
These updates reflect a shift toward both adaptability and accountability, ensuring that businesses not only meet compliance standards but also maintain robust security over time.
What should I do first to be ready by March 31, 2025?
To get ready for the March 31, 2025 deadline, it's important to focus on meeting the requirements of PCI DSS v4.0, particularly the "future-dated" controls. Here's how you can approach it:
- Review future-dated controls: Carefully examine and implement all security measures that are labeled as future-dated under PCI DSS v4.0.
- Enhance authentication: Strengthen your systems with multi-factor authentication (MFA) and ensure password policies align with updated standards.
- Perform a risk analysis: Assess potential risks, tailor your security controls accordingly, and document your strategy for implementation.
- Verify compliance: Regularly test your systems and processes to confirm compliance with all required standards.
Taking these steps will help ensure you're prepared and aligned with the updated requirements.
How can I reduce PCI scope to lower compliance costs?
To make PCI compliance more manageable and cost-effective, you can use methods like tokenization, network segmentation, and cutting down on unnecessary data storage. Tokenization swaps out sensitive card data with secure tokens, which limits the number of systems subject to PCI requirements. Network segmentation helps by isolating environments that handle cardholder data, reducing exposure. Additionally, storing less data and outsourcing specific processes can simplify compliance efforts and reduce expenses.
