Behavioral Biometrics in Fraud Prevention Explained
Behavioral biometrics is reshaping how fraud is detected by monitoring how users interact with devices, rather than relying solely on passwords or physical identifiers. This method tracks unique behaviors like typing patterns, mouse movements, and touchscreen gestures to identify potential fraud in real time. Unlike static security methods, it continuously analyzes user behavior throughout a session, making it harder for attackers to bypass.
Key Points:
- What It Is: Behavioral biometrics analyzes user interaction patterns, such as typing speed, mouse paths, and touch pressure.
- How It Works: It creates a behavioral profile and flags deviations during a session, using machine learning to detect risks.
- Why It Matters: Prevents account takeovers, bot attacks, and transaction fraud by identifying behaviors attackers can't replicate.
- Market Growth: Expected to grow from $2.98 billion in 2024 to $18.39 billion by 2033, driven by rising fraud threats.
- Privacy Focus: Works silently in the background without storing sensitive personal data.
By tracking subtle, hard-to-mimic behaviors, this approach strengthens security while maintaining a smooth user experience.
Revolutionizing Fraud Prevention with Behavioral Intelligence
sbb-itb-5d40823
How Behavioral Biometrics Work
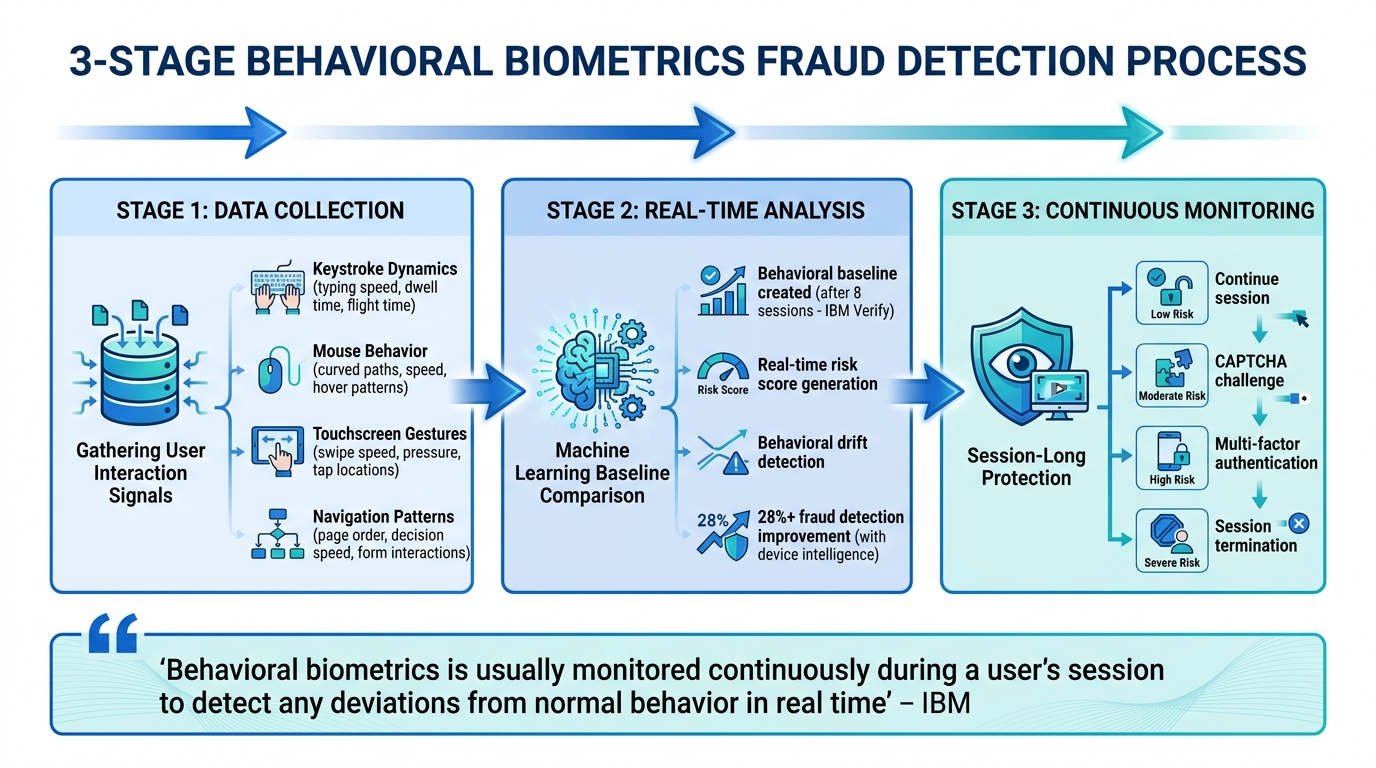
How Behavioral Biometrics Work: 3-Stage Fraud Detection Process
Behavioral biometrics operate through three main stages: collecting interaction data, analyzing it against established user patterns, and continuously monitoring activity during the session. This process runs seamlessly in the background, offering an added layer of security without requiring extra effort from users. By distinguishing genuine user behavior from fraudulent activity, this technology effectively detects and prevents fraud.
Data Collection and Input Signals
Behavioral biometrics gather data from various user interactions, creating a detailed profile of typical behavior. Here’s how it works across different input methods:
Keystroke Dynamics
Keystroke analysis captures how users type, including their speed, rhythm, and patterns like "dwell time" (how long a key is pressed) and "flight time" (the gap between key presses). Other factors, such as error rates, backspace usage, and the use of shift keys, also contribute to building a behavioral profile [3].
Mouse and Cursor Behavior
Mouse movements reveal unique human traits. Humans tend to create curved, inconsistent paths, while bots often follow straight, precise lines. Systems also assess cursor speed, acceleration, and subtle pauses. Even how users approach buttons or links and the time they hover before clicking can differentiate human behavior from automated scripts [3].
Touchscreen Interactions
On mobile devices, touchscreen gestures like swipe speed, screen pressure, tap locations, and scrolling direction provide valuable insights. These details can even identify whether someone is left- or right-handed. Additionally, device sensor data - from accelerometers and gyroscopes - tracks phone angles, rotation, and grip force, adding another layer of behavioral detail [7].
Navigation and Cognitive Patterns
The way users navigate websites or apps offers further clues. Systems monitor the order of page visits, time spent on fields, and "decision speed" - how quickly users interact with familiar interfaces. Fraudulent behavior might show hesitation or unusual navigation patterns. Form interactions are also analyzed for red flags, such as instant field completion (copy-pasting), perfectly timed intervals, or skipping common steps like reviewing terms and conditions [3].
| Signal | Human Pattern | Bot/Fraudster Pattern |
|---|---|---|
| Mouse Movement | Curved paths with variable speeds | Straight lines, constant speed, or jumps |
| Typing Timing | Delays between 200ms–8s | Consistent or random uniform delays |
| Form Entry | 4–15 seconds (typed from memory) | Less than 1 second (pasted data) |
| Navigation | Selective, interest-driven visits | Systematic or alphabetical patterns |
These signals are continuously collected and analyzed to identify irregularities in real time.
Real-Time Anomaly Detection
Once the system gathers initial data, machine learning algorithms - like deep learning models - create a behavioral baseline. For example, IBM Verify establishes this baseline after just eight user sessions [1].
During each interaction, the system compares current behavior to the baseline, generating a real-time risk score. Deviations, or "behavioral drift", are flagged when current actions stray from established patterns. This might include differences in motor habits, timing, or navigation speed [3]. Bots and fraudsters are often exposed by their inability to mimic natural human behaviors, such as micro-hesitations or irregular mouse movements [3].
Behavioral biometrics combined with device intelligence can enhance fraud detection rates by over 28% [6]. This technology is particularly effective at identifying new threats, such as unfamiliar Remote Access Trojans or emulators, because their interaction styles inherently differ from legitimate users [7].
When anomalies are detected, the system doesn’t stop there - it continues monitoring throughout the session to ensure ongoing protection.
Continuous Session Monitoring
Instead of relying solely on login verification, behavioral biometrics monitor user activity throughout the session. This approach strengthens security without requiring additional input from the user.
The system evaluates every action in real time, updating fraud scores as the session progresses. If the score crosses a certain threshold, the platform can respond immediately - injecting a CAPTCHA for minor risks, requesting multi-factor authentication for higher risks, or terminating the session altogether for severe deviations [3]. This is particularly effective against threats like session hijacking, where a different user or bot takes over after a legitimate login [4].
IBM emphasizes:
Behavioral biometrics is usually monitored continuously during a user's session to detect any deviations from normal behavior in real time [1]
This continuous monitoring is vital for combating account takeover attacks, which make up around 27% of global fraud cases [5]. By identifying behavioral drift throughout the session, these systems catch threats that traditional, one-time authentication methods might miss.
Applications of Behavioral Biometrics in Fraud Prevention
Behavioral biometrics helps combat fraud in various scenarios, from stolen credentials to automated bot attacks. By examining how users interact with digital platforms, this technology identifies fraudsters even when traditional security tools fail.
Preventing Account Takeovers
In 2024, account takeover fraud cost U.S. adults roughly $15.6 billion, a 23% rise compared to the previous year [11]. Over 80% of these cases involved stolen or compromised credentials, allowing fraudsters to log in with valid passwords [2].
Behavioral biometrics addresses this by monitoring user behavior throughout the session, not just at login. Even if an attacker uses the correct credentials, their actions - like changing account settings, resetting passwords, or adding beneficiaries - can reveal malicious intent. Genuine users, on the other hand, navigate with natural hesitation and familiarity.
The system identifies "behavioral drift", or deviations from a user’s typical patterns. For instance, while a fraudster might know what to input, their process of getting there often differs. This includes subtle cues like unusual typing rhythms, erratic mouse movements, or fragmented typing that could indicate stress or coercion [2][9].
"Credentials were never designed to prove intent. They only prove access." – Amit Chahal, Co-founder & Head of Data Science, Sign3 [9]
Advanced tools can also detect when devices are hijacked by Remote Access Trojans (RATs) or bots, recognizing unnatural cursor movements or perfectly timed keystrokes [2].
These capabilities extend seamlessly to identifying fraud during account creation.
Detecting New Account Fraud
In 2024, first-party fraud made up 36% of all reported global fraud cases [5]. Behavioral biometrics plays a key role in spotting fraudulent activity during account creation. Bots, for example, often display uniform cursor movements, consistent keystroke delays, and robotic navigation patterns that bypass CAPTCHAs [2][7]. Fraud rings may also copy-paste data into multiple fields - a behavior rarely seen in legitimate users, who tend to type details or use auto-fill [2].
The technology can also detect synthetic identities - fake profiles created using real data fragments. While these profiles may pass traditional Know Your Customer (KYC) checks, their overly polished or mechanical behavior raises red flags [2]. Fraudsters often skip steps like reading terms and conditions or reviewing policies, actions that behavioral systems monitor closely [7].
Organizations also analyze form completion times to catch "rush behavior", where applications are filled out impossibly fast for manual entry. In 2024, 79% of U.S. organizations reported facing payment fraud attempts [12].
Identifying synthetic identities and rushed entries helps pave the way for blocking fraudulent transactions.
Blocking Transaction Fraud
Behavioral biometrics doesn’t stop at monitoring sessions - it also evaluates individual transactions. By comparing current actions against a user’s established behavior, the system assigns a risk score [15][10]. This approach is particularly effective against carding, where stolen credit cards are tested on e-commerce sites. For instance, legitimate users typically take 4–15 seconds to input card details, while fraudsters often complete the task in under a second [10]. Fraudsters also tend to use straight-line mouse movements and instant clicks, unlike the more natural, curved paths of genuine users.
When risk scores exceed certain thresholds, the system can take actions like approving the transaction, triggering additional authentication (e.g., fingerprint scans), or blocking the transaction altogether [13][14][5]. By mid-2025, BioCatch was protecting over 525 million individuals across more than 280 financial institutions, analyzing over 15 billion user sessions monthly to detect anomalies and prevent fraud in real time [5]. Combining behavioral data with device fingerprinting has been shown to boost fraud detection rates by over 28% [15].
Benefits of Behavioral Biometrics
Behavioral biometrics takes security to the next level by analyzing how users interact with systems rather than relying on static credentials like passwords or device IDs. This method focuses on unique digital behaviors - such as typing patterns, mouse movements, or swipe pressure - creating a security layer that's incredibly difficult to mimic [2][8]. Beyond enhancing security, it also improves the user experience by operating seamlessly in the background.
Better Fraud Detection Accuracy
One of the standout strengths of behavioral biometrics is its ability to monitor user behavior throughout an entire session. This continuous observation enables it to detect mid-session account takeovers and Remote Access Trojan (RAT) attacks that traditional systems often miss [5][7]. By identifying deviations from a user’s typical behavior - known as behavioral drift - it can flag potential fraud in real time [3].
A major advantage is its ability to differentiate bots from humans. Behavioral patterns, like how a person types or moves their mouse, are incredibly hard for bots to replicate. This even allows the system to identify zero-day threats by recognizing unusual behavior, even when the specific attack method is unfamiliar [3][7].
"The core insight of behavioral biometrics is that behavior is harder to fake than identity." – ClickStream Research [3]
This precise detection helps prevent fraud while also reducing unnecessary alerts, creating a more efficient security system.
Fewer False Positives
Traditional security systems often flag legitimate users as potential threats, especially if their behavior deviates from global averages. Behavioral biometrics avoids this issue by comparing users against their own unique patterns, making it especially effective for identifying power users who might otherwise be mistaken for bots [3][7].
The system uses confidence stacking, which requires multiple behavioral signals to align before triggering a fraud alert. This ensures that no single anomaly results in a false block [3]. It also uses contextual intelligence to differentiate between a legitimate user in a hurry and a malicious script by analyzing the flow and style of interactions [2].
Instead of outright blocking suspicious activity, the system adapts its response based on risk levels. For example:
- Moderate risk might prompt a CAPTCHA or SMS verification.
- High risk could lead to transaction blocks [3][8].
Over time, consistent legitimate behavior builds trust, further reducing the chances of false positives [3].
Frictionless User Experience
One of the most user-friendly aspects of behavioral biometrics is its ability to work silently in the background. It analyzes micro-interactions without requiring any extra steps from users [3][7][5]. This "silent authentication" ensures security without disrupting the user experience [8][5].
"The best cybersecurity is the kind customers never notice." – Focal [8]
Because behavioral biometrics minimizes false positives, users rarely encounter additional verification steps, making interactions smoother. While traditional credentials confirm access, behavioral signals validate intent by ensuring that current actions align with a user’s established profile. Only when a high-risk score is detected does the system prompt step-up authentication, allowing low-risk users to continue uninterrupted [3].
Additionally, this approach is designed with privacy in mind. Instead of collecting sensitive personal information, it focuses on interaction patterns like rhythm and timing. This helps organizations comply with regulations like the EU’s PSD2, which recognizes behavioral traits as valid authentication factors under Strong Customer Authentication requirements [2][5].
Best Practices for Implementing Behavioral Biometrics
Implementing behavioral biometrics effectively takes careful planning to ensure a balance between security, privacy, and user experience. Without a thoughtful approach, organizations risk issues like false positives or leaving critical vulnerabilities exposed.
Start with High-Risk Areas
Focus on securing high-risk touchpoints first - these are the areas where fraud can cause the most harm. For example, login pages are a prime target, as over 80% of confirmed account takeover incidents in 2025 were linked to stolen or compromised credentials rather than brute-force attacks[9]. Similarly, account creation pages are critical since law enforcement identified 1.9 million money mule accounts in 2025, with this type of fraud growing 20 times faster than other fraud types[9].
Financial transactions and checkout processes also need immediate attention. One mid-sized fintech in 2025 successfully stopped a high-value executive transfer when behavioral biometrics flagged unusual cursor movements and navigation patterns. Even though the credentials and device were legitimate, the system detected coercion and paused the transfer[9].
Other sensitive areas, such as account management features where users update passwords, beneficiaries, or contact details, are often the first targets in account takeover attempts. IBM's Verify solution, for instance, uses data from at least eight sessions to establish a behavioral baseline, reducing false positives and improving detection accuracy[1][8][10].
Securing these critical points is essential, but it must go hand-in-hand with robust privacy measures.
Protect Privacy and Data Security
Once you've addressed high-risk areas, securing behavioral data becomes the next priority to maintain user trust. With the average cost of a data breach reaching $4.88 million in 2024[16], and GDPR fines totaling EUR 1.2 billion that same year[5], protecting data is not just a best practice - it’s a necessity.
One effective approach is transforming raw behavioral inputs into compact mathematical vectors directly on the client side. This ensures sensitive details like keystrokes or field contents are neither transmitted nor stored[16]. Instead, the system captures how users interact - focusing on rhythm, timing, and pressure rather than the actual content they type[8].
To safeguard this data, use modern TLS for data in transit and strong encryption keys with regular rotation for data at rest. Limit the use of collected behavioral data strictly to fraud prevention and security purposes to comply with GDPR and CCPA regulations[16][13][17].
"Behavioral biometrics is a potent tool for preventing fraud. However, using it means we must protect user data carefully." – Feedzai[13]
Additionally, employ least-privilege access roles, administrative SSO, and secure storage to restrict data access to only authorized personnel[16][17]. Transparency is key - clearly communicate how the system works, what data is collected, and how it will be used to build trust with users[17].
Combine with Existing Fraud Prevention Tools
After securing high-risk areas and ensuring data privacy, behavioral biometrics should be integrated into a broader fraud prevention strategy. This technology is most effective when paired with other tools. For instance, combining behavioral biometrics with digital identity and device intelligence has been shown to boost fraud detection rates by over 28%[15].
Layer behavioral biometrics with other methods like device fingerprinting, IP analysis, and physical biometrics for a well-rounded security approach. Real-time risk scoring can trigger additional authentication steps - like multi-factor authentication (MFA) or CAPTCHA - only when anomalies are detected. This ensures legitimate users enjoy a seamless experience. Systems capable of computing behavioral scores in real time (under 3ms) can block bots and carding attempts before they even begin[10].
Instead of outright blocking suspicious activity, consider using graduated responses based on risk levels. For example, moderate risks might prompt a CAPTCHA, while high-risk scenarios could require manual review.
Conclusion
Behavioral biometrics play a key role in AI-driven transaction dispute recovery, offering a fresh approach to fraud prevention by focusing on "who you are" through your digital behavior instead of relying solely on "what you know" or "what you have" [2]. Unlike traditional security methods that verify identity only at login, this technology provides continuous authentication throughout a session. This makes it effective at catching threats that bypass passwords and physical biometrics [1]. Such ongoing monitoring not only identifies risks in real time but also lays the groundwork for a forward-thinking fraud prevention strategy.
The numbers tell a compelling story: the behavioral biometrics market is expected to grow to $18.39 billion by 2033 [5], while global fraud losses are projected to reach $534 billion by 2025 [9]. Behavioral biometrics excel at addressing advanced threats, including account takeovers - which made up 27% of fraud cases in 2024 [5] - as well as bot attacks and social engineering schemes.
What makes this technology stand out is its seamless and privacy-conscious design. It works passively in the background, analyzing behaviors like keystrokes, mouse movements, or touchscreen swipes without interrupting the user experience or storing sensitive personal data [7]. For the best results, start by implementing it in high-risk areas like login screens and payment gateways. Pairing it with existing tools - such as device fingerprinting and digital identity verification - can further strengthen your security framework. Maya Ogranovitch Scott from Ping Identity highlights its importance:
Behavioral biometrics, used in conjunction with physical biometrics and other security measures, can greatly improve an organization's security posture and help effectively fight fraud and decrease risk – while offering a smooth experience to trusted users [7].
As AI-powered threats become more advanced - potentially reducing exploitation time by 50% [1] - behavioral biometrics rise to meet the challenge. By identifying patterns that attackers can't mimic, even with valid credentials [3], this technology builds a security system that adapts and strengthens with each interaction.
FAQs
Does behavioral biometrics track what I type?
Behavioral biometrics analyze how you type - focusing on aspects like keystroke speed, rhythm, and pressure. By studying these patterns, it can identify you and differentiate your behavior from that of potential fraudsters.
How quickly can it detect an account takeover mid-session?
Behavioral biometrics can spot account takeover attempts almost instantly. By monitoring patterns such as typing speed, mouse movements, and device details, it identifies unusual behavior and raises alerts in real time, often within seconds.
What should businesses integrate it with for best results?
For the best outcomes, businesses should integrate behavioral biometrics with traditional security measures like passwords, PINs, or multi-factor authentication (MFA). Adding tools like device intelligence and real-time monitoring can further enhance security by spotting unusual behaviors - think irregular typing rhythms or odd mouse movements - that might signal fraud. This layered strategy not only strengthens protection but also minimizes false alarms and keeps the user experience smooth by authenticating discreetly in the background.
