Account Takeover (ATO) Attacks: 2026 Trends
Account Takeover (ATO) attacks are surging in 2026, with fraudsters using advanced AI tools to bypass security measures and target consumer accounts. Losses are projected to hit $17 billion globally this year, fueled by techniques like credential stuffing, phishing-as-a-service, and session hijacking. Here's what you need to know:
- Key Stats: 83% of businesses faced ATO incidents in 2025, and 21% of consumers were affected. Victims spend an average of 17 hours resolving these issues.
- Attack Methods: AI bots now mimic human behavior, deepfake technology enables identity impersonation, and MFA fatigue attacks exploit user frustration.
- Industries at Risk: Fintech, travel, and mid-market retailers are seeing the sharpest increases in ATO attempts.
- Defense Strategies: Behavioral biometrics, modern MFA methods, and credential monitoring tools are critical for detecting and preventing ATO attacks.
- Recovery Tools: Platforms like DidIBuyIt streamline dispute processes, helping users recover funds efficiently.
Protecting accounts now requires layered security, AI-powered defenses, and swift recovery plans. These measures are vital to staying ahead of increasingly sophisticated fraud tactics.
Cyber Trends in 2026: Attackers Don’t Hack Anymore, They Log In
sbb-itb-5d40823
ATO Attack Trends and Statistics for 2026
Account Takeover Attack Statistics and Trends 2021-2026
Growth in ATO Incidents from 2021 to 2026
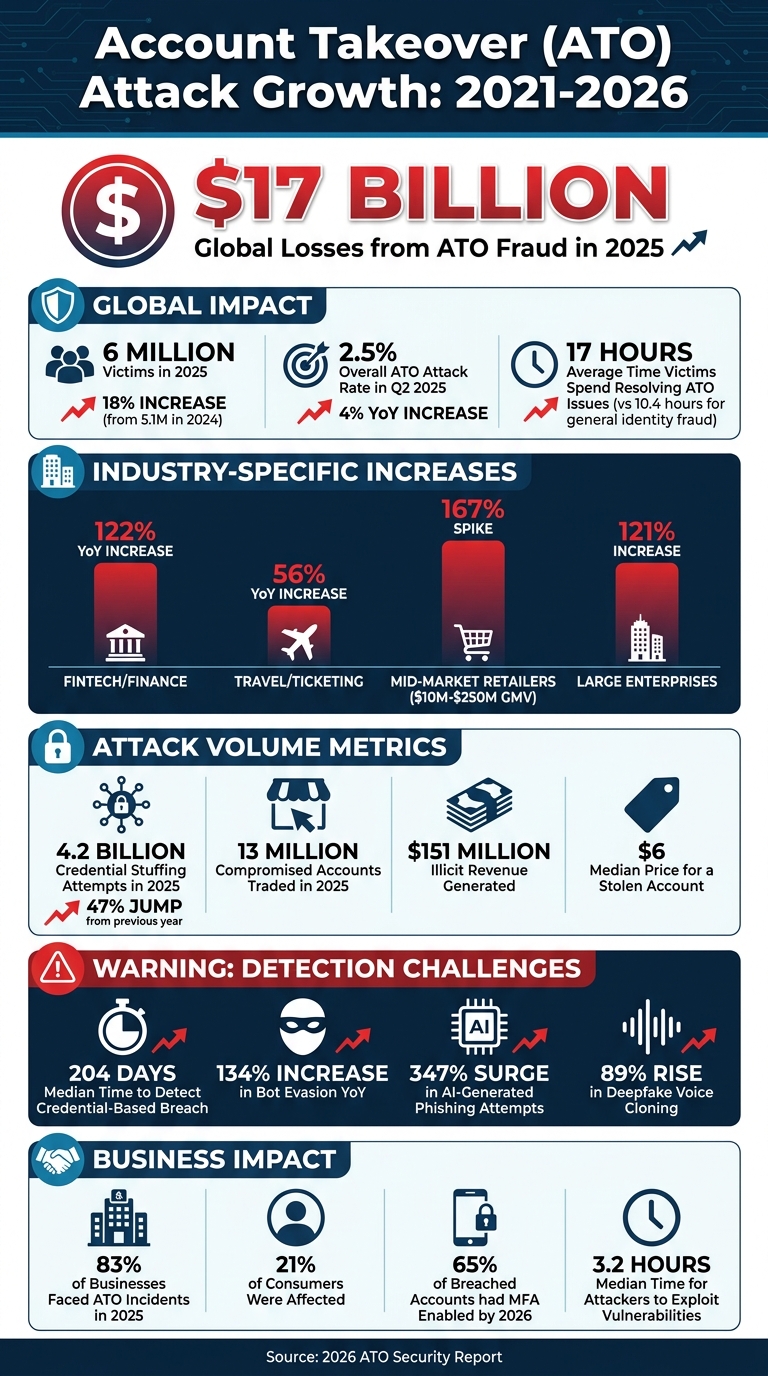
The data paints a concerning picture. Global losses from ATO fraud reached $17 billion in 2025, up from $13 billion in 2024 [4]. The number of victims rose to 6 million in 2025, an 18% increase compared to 5.1 million in 2024 [5]. The overall ATO attack rate also climbed to 2.5% in Q2 2025, reflecting a 4% increase year-over-year [4].
Certain industries experienced even sharper surges. Fintech and finance saw a staggering 122% rise in ATO attacks year-over-year, while the travel and ticketing sector recorded a 56% increase. Mid-market retailers - those generating $10 million to $250 million in gross merchandise value - faced a 167% spike in attacks, compared to a 121% rise for larger enterprises [3][4]. Credential stuffing attempts also skyrocketed, with 4.2 billion attempts in 2025, a 47% jump from the previous year [8].
The impact extends beyond financial losses. Victims now spend an average of 17 hours resolving ATO-related issues, a significant jump from the 10.4 hours typically required for general identity fraud [5]. Meanwhile, criminal marketplaces traded around 13 million compromised accounts in 2025, generating $151 million in illicit revenue. Shockingly, the median price for a stolen account was just $6 [6]. These escalating figures underscore the urgency of addressing the forces behind this growth.
What's Driving the Increase in ATO Attacks
Three major factors are fueling this rise in ATO attacks.
First, password reuse remains a widespread issue. A striking 62% of Americans admit to reusing passwords across multiple accounts, and 52% of all login attempts now involve leaked credentials [7]. This habit provides cybercriminals with an expansive attack surface, especially given the availability of billions of stolen username-password combinations.
Second, the rise of Fraud-as-a-Service has made cybercrime more accessible than ever. Tools like phishing kits, botnets, and AI-powered software are now readily available on the dark web, allowing even non-technical criminals to execute complex attacks. Brittany Allen, Senior Trust and Safety Architect at Sift, explains:
Agentic AI lowers the barrier to fraud by making powerful tools accessible to virtually anyone [4].
These advanced AI systems can simulate legitimate user behavior, such as mimicking device movements and purchase patterns, in real time [1][4].
Finally, enhanced checkout security measures have pushed fraudsters to focus on login stages, where compromised accounts offer access to stored payment details, loyalty rewards, and personal information. Alexander Hall, Trust and Safety Architect at Sift, notes:
Fraudsters aren't just exploiting weak spots, they're innovating faster than many companies can adapt [4].
The challenges of detection are growing, with bot evasion increasing by 134% year-over-year, AI-generated phishing attempts surging by 347%, and deepfake voice cloning rising by 89% [8]. Alarmingly, the median time to detect a credential-based breach is 204 days, giving attackers over six months to operate undetected [8].
Common ATO Attack Methods in 2026
Credential Stuffing and Phishing-as-a-Service
Launching an Account Takeover (ATO) campaign no longer requires sophisticated hacking skills. Platforms offering Phishing-as-a-Service (PhaaS) have made these attacks more accessible, with ready-made kits like Evilginx2, Tycoon, Mamba, and Typhoon 2FA readily available on the dark web [9][12]. These tools enable Adversary-in-the-Middle (AiTM) attacks, which intercept login credentials and multi-factor authentication (MFA) responses in real time through fake login pages.
Attackers often rely on massive collections of stolen username-password combinations. Adding to the complexity, modern AI bots are now capable of mimicking legitimate user behavior. These bots simulate realistic patterns, such as natural device movements or typical purchase times, making it incredibly difficult to distinguish them from actual customers [1].
"Logging in is now faster, cheaper, and more reliable than breaking in." - ByteVanguard [9]
Emerging deepfake technologies are taking these threats to an entirely new level.
AI-Generated Deepfakes and Identity Impersonation
What was once a hypothetical concern has become a daily challenge: deepfake technology. In 2025 alone, deepfake fraud attempts skyrocketed by 1,300%, costing U.S. businesses $1.1 billion - a staggering 300% increase from previous years [12]. Attackers are now using AI-powered speech cloning to bypass biometric phone verification systems. For example, voice impersonation attacks rose 149% at banks and 475% at insurance companies in 2025 [12].
One alarming case involved a finance worker transferring $25 million after being duped by a video call featuring deepfaked company executives [12]. This form of CEO fraud now impacts around 400 companies every single day [12]. Attackers also exploit customer support systems by using synthetic voices to deceive staff into resetting MFA settings or modifying account recovery options [12].
But impersonation isn’t the only concern - attackers are also exploiting session vulnerabilities to bypass security.
Session Hijacking and MFA Fatigue Attacks
By 2026, a surprising 65% of breached accounts already had MFA enabled [13]. This shift has pushed attackers to focus on more advanced techniques, such as session hijacking. Using malware to steal session cookies, authentication tokens, and browser fingerprints, attackers can bypass MFA and gain trusted session access [10][11].
Another growing threat is MFA fatigue attacks, also known as push bombing. In these attacks, users are bombarded with repeated push notifications until they eventually click "Approve" out of frustration [12][14]. Additionally, OAuth token abuse has become a significant issue, with attackers leveraging a single compromised identity to maintain access across multiple connected SaaS platforms. In 2026, 67% of initial access incidents stemmed from identity and session-based compromises [11]. Alarmingly, the median time for attackers to exploit these vulnerabilities is now just 3.2 hours [11].
"Passing MFA does not mean the session is safe." - Jason Wagner, Constella Intelligence [10]
AI-Powered Tools to Prevent ATO Attacks
As the techniques behind account takeover (ATO) attacks evolve, AI-powered tools have stepped up to provide real-time, continuous protection. These tools analyze user behaviors - like typing rhythm and mouse movements - to create unique profiles. When deviations are detected, they can trigger extra verification steps, restrict risky actions (like wire transfers), or even terminate active sessions. Let’s explore three key tools shaping the defense against ATO attacks: behavioral biometrics, adaptive MFA, and credential monitoring.
Behavioral Biometrics and Real-Time Monitoring
Traditional security measures often stop at login, but behavioral biometrics go further by continuously analyzing how users interact with their devices. These systems monitor factors like typing cadence, navigation speed, device handling, and even touch pressure on mobile screens. If someone with stolen credentials logs in but exhibits unusual behaviors - like inconsistent typing patterns or awkward navigation - the system flags the activity.
"Account takeovers do not announce themselves. They blend in." - James Savard, IRONSCALES [15]
Behavioral biometrics can also detect signs of coaching, such as guided mouse movements or abnormal typing rhythms, and immediately alert security teams. In 2025, companies using behavioral AI reported saving an average of 1,454 hours annually on manual fraud investigations [17]. These systems boast accuracy rates of 90% to 95% in distinguishing legitimate users from attackers [3].
Modern MFA Methods and Passwordless Login
The vulnerabilities of SMS-based authentication have driven many organizations to adopt passkeys based on the FIDO2 standard. These passkeys store credentials locally, offering a more secure alternative. For example, Best Buy’s 2024 switch to passkeys boosted returning-customer sign-in rates from 20% to over 90% [3].
Adaptive MFA takes security a step further by only challenging users when suspicious activity is detected - such as logging in from a new device, accessing from an unusual location, or using a risky IP address. This method ensures a smooth experience for 95–98% of legitimate users [3]. Combined with tools like hardware security keys and authenticator apps, adaptive MFA makes credential stuffing attacks far less effective.
Credential Monitoring and Breach Alerts
Without realizing it, your credentials could already be circulating on underground forums. Credential monitoring tools work around the clock, scanning paste sites, breach databases, and dark web forums for compromised usernames, passwords, and email addresses [16]. When leaks are detected, these tools issue immediate alerts and can automatically initiate protective actions, such as password resets or session terminations.
SpyCloud is a standout example, offering automated remediation by continuously monitoring for exposed identity data and triggering defenses when necessary [16]. Some platforms even use shared fraud signals across networks, ensuring that a flagged device is treated as high risk across multiple organizations.
How to Recover from ATO Attacks: Disputing Fraudulent Transactions
Once you've put prevention measures in place, knowing how to recover quickly from an Account Takeover (ATO) attack is just as important. With these attacks becoming more advanced, a well-thought-out recovery plan can make all the difference.
How to Spot and Report Fraudulent Charges
Start by reviewing your transaction history for anything that seems off - especially small, unfamiliar charges. These can sometimes be "test runs" by fraudsters.
If you spot unauthorized electronic fund transfers, report them to your bank or card issuer immediately. Under Regulation E, how much you're liable for often depends on how quickly you act [19]. It's important to note that credit bureaus are generally involved in cases of new-account fraud, not disputes over existing accounts [19]. Most banks and card networks enforce a strict 120-day deadline to dispute charges, so acting fast is essential. Once that window closes, recovering your money becomes almost impossible [21].
Before contacting your bank, gather all the evidence you can. This might include transaction logs, screenshots of the charges, and any communications with merchants. A strong dispute case hinges on presenting a thorough and well-documented evidence package, along with your confirmation that you didn’t authorize the transactions [19].
Using DidIBuyIt for ATO Dispute Recovery
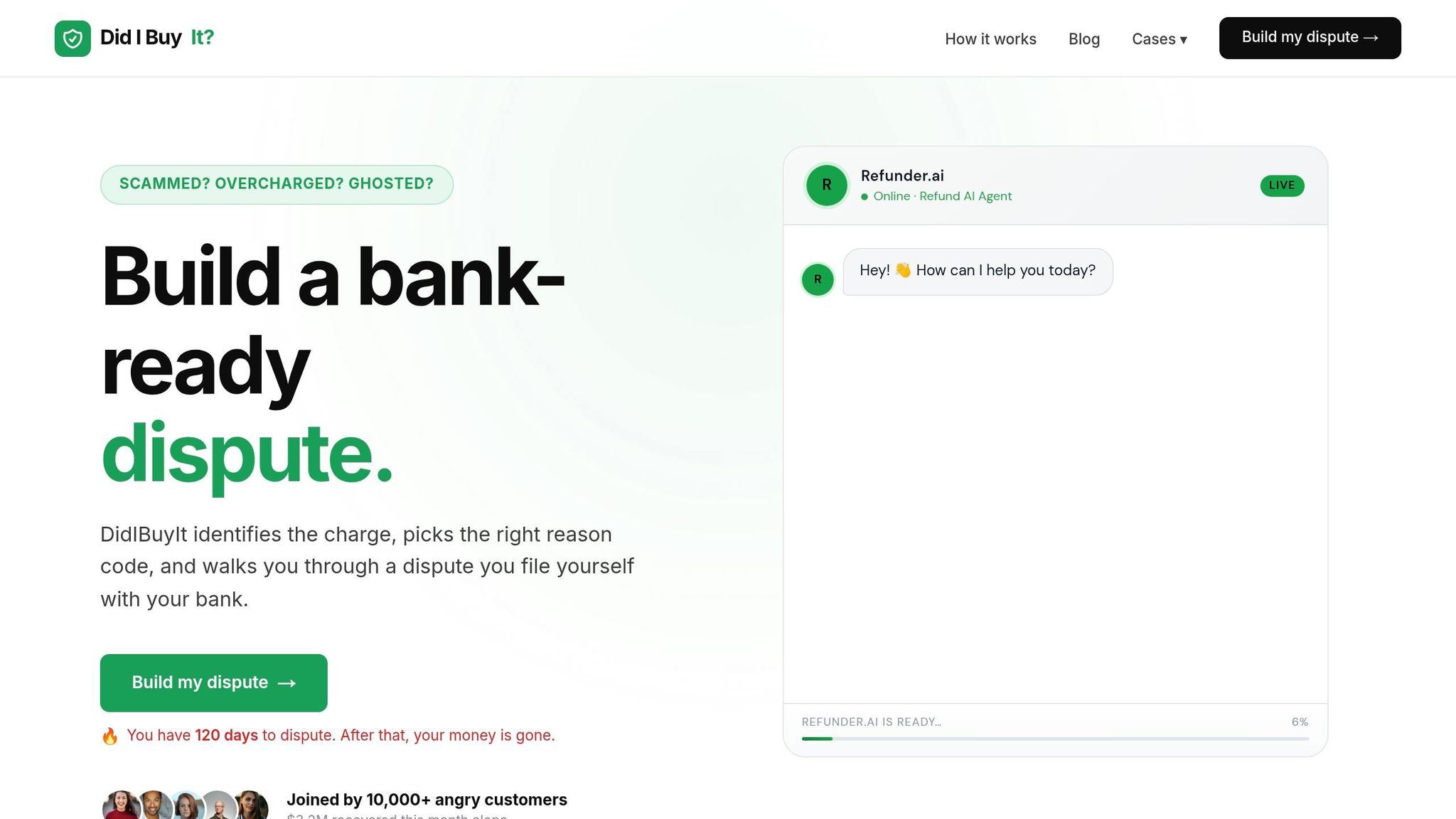
DidIBuyIt is an AI-powered platform designed to streamline the dispute process. In less than three minutes, it analyzes your case, identifies the strongest dispute angle, and ensures the correct bank reason code is used [20][21]. This last step is critical since disputes are often denied when the wrong reason code is submitted [20][21].
The platform provides a personalized "battle plan" that includes an evidence checklist, key bank regulations (like Visa and Mastercard rules), and even an estimate of your chances for success [20]. You'll also receive a pre-prepared PDF dispute letter and scripts for communicating with banks or merchants [20][21]. For instance, in May 2026, Sarah M. successfully recovered $599 from Adobe after being wrongly charged for a subscription she had canceled three months earlier. Using DidIBuyIt, she built her case in minutes, and her bank reversed the charge within six days [21].
DidIBuyIt supports disputes across all major card networks, including Visa, Mastercard, Amex, and Discover, as well as platforms like PayPal, Apple Pay, and Venmo. Impressively, 94% of users recover funds they didn’t even realize they were owed, with customers collectively recovering $3.2 million in just one month [21].
DidIBuyIt Plans: Basic Recovery vs. Advanced Support
To address different recovery needs, DidIBuyIt offers two service tiers:
| Plan Name | Price | Description/Tagline | Features |
|---|---|---|---|
| Basic Recovery | Flat Fee | AI-powered dispute analysis and guidance | AI analysis, bank-ready documents, step-by-step guidance, encrypted data |
| Advanced Support | Flat Fee | Enhanced support for complex disputes | All Basic Recovery features, plus priority support and advanced evidence preparation |
The Advanced Support plan stands out by automating reason code identification and evidence compilation, making it especially helpful for more complicated disputes. For disputes under $1,000, both plans provide an affordable and efficient solution.
Take Daniel K.'s case from April 2026: He recovered $320 from a PayPal seller who had vanished with his funds. Although PayPal initially sided with the seller, Daniel used DidIBuyIt to identify the exact reason code his bank required, leading to a full refund within two weeks [21].
Whether you're facing a straightforward or complex dispute, DidIBuyIt simplifies the process and increases your chances of success.
Conclusion: Protecting Yourself Against ATO Attacks in 2026
Relying solely on stronger passwords won’t cut it when it comes to preventing account takeover (ATO) attacks. With these incidents impacting most organizations and costs skyrocketing into the billions, a multi-layered defense strategy is now a must. This includes phishing-resistant passkeys, adaptive multi-factor authentication (MFA), device intelligence, and behavioral biometrics to stay ahead of attackers [3].
"Account takeover is no longer a fraud-team problem you can solve with stronger password rules. It is a security architecture problem that needs a layered stack." - Andrew Agarwal, Security Analyst [3]
Consumers are already on board with these measures. A whopping 93% are willing to go through extra verification steps during login if it means reducing fraud risk [2]. Even more compelling, accounts secured with passkeys reported zero confirmed credential-phishing takeovers in deployments tracked by the FIDO Alliance in 2025 [3]. Transitioning to phishing-resistant authentication isn’t just about better security - it’s also aligning with user expectations.
Still, no system is foolproof. Even the most robust defenses can be breached. When that happens, quick recovery becomes critical. With the average ATO incident costing over $12,000 [18], tools like DidIBuyIt are game-changers. This AI-powered platform offers fast dispute resolution by analyzing your case, generating professional bank-ready documentation, and providing step-by-step guidance to help you recover your funds efficiently.
In 2026, combining advanced security measures with swift, AI-driven recovery solutions isn’t just a precaution - it’s essential for safeguarding your finances.
FAQs
How can I tell if my session was hijacked even with MFA on?
Watch for unusual activity in your account, like actions you didn’t authorize, logins from unknown devices or locations, or strange browser behavior. Attackers can sometimes bypass MFA by exploiting session tokens or cookies, so it’s important to stay vigilant. If something feels off, take immediate steps to secure your account.
What’s the fastest way to lock down my accounts after an ATO?
To regain control of your accounts after an Account Takeover (ATO), take these steps as quickly as possible:
- Change your passwords on all compromised accounts right away. Use strong and unique passwords for each.
- Enable multi-factor authentication (MFA) if it’s not already set up. Opt for phishing-resistant methods for better protection.
- Revoke active sessions and devices to immediately cut off access for the attacker.
- Monitor account activity closely for any unusual behavior or unauthorized changes, and report anything suspicious.
- Update security settings and double-check your recovery options to make sure they’re secure.
What evidence should I collect to win a bank dispute for ATO charges?
To build a strong case in a bank dispute over ATO charges, you'll need to collect evidence that highlights unauthorized access or fraudulent activity. Key items to gather include:
- Transaction records that show unfamiliar or suspicious activity on your account.
- Account access logs indicating unusual login times or locations.
- Bank alerts or communications flagging suspicious activity.
Additionally, make sure to provide proof of account ownership, such as ID documents, and include any correspondence you've had with the bank regarding the dispute. These details can help substantiate your claim.